diff --git a/.gdb_history b/.gdb_history
deleted file mode 100644
index 4846c14..0000000
--- a/.gdb_history
+++ /dev/null
@@ -1,61 +0,0 @@
-b ContactDataStore::dump()
-r
-n
-q
-b ContactDataStore::dump()
-r
-n
-c
-./build.sh
-$(./build.sh)
-$(./build.sh)
-q
-r
-q
-r
-b ContactDataStore::dump()
-r
-n
-b ContactItem::toJson()
-r
-c
-n
-q
-b ContactItem::toJson()
-r
-n
-c
-c
-c
-c
-c
-c
-c
-c
-q
-b FileSystem::writeContacts(QString file, json j)
-b FileSystem::writeContacts
-r
-q
-b FileSystem::writeContacts
-r
-b ContactDataStore::dump()
-r
-c
-n
-q
-b FileSystem::writeContacts
-r
-n
-q
-r
-b FileEncryption::encrypt
-r
-s
-n
-q
-b FileSystem::readContactsOldFormat
-r
-n
-c
-q
diff --git a/.gitignore b/.gitignore
index e0ad3e6..f5e679c 100644
--- a/.gitignore
+++ b/.gitignore
@@ -40,4 +40,5 @@ silentdragonlite.pro.user.4.10-pre1
silentdragonlite
silentdragonlite_plugin_import.cpp
silentdragonlite_resource.rc
-SilentDragonLite
\ No newline at end of file
+SilentDragonLite
+.gdb_history
diff --git a/.travis.yml b/.travis.yml
index 443442f..0651152 100644
--- a/.travis.yml
+++ b/.travis.yml
@@ -1,26 +1,22 @@
- language: rust
+language: rust
+
matrix:
include:
# works on Precise and Trusty
- os: linux
- dist: xenial
compiler: clang
-
-
addons:
apt:
sources: ['ubuntu-toolchain-r-test', 'llvm-toolchain-precise-3.7']
packages: ['clang-3.7', 'g++-5']
-
-
-
before_script:
-- export PATH="$PATH:$HOME/.cargo/bin"
+ - export PATH="$PATH:$HOME/.cargo/bin"
before_install:
-
+ - rustup component add rustfmt --toolchain stable-x86_64-unknown-linux-gnu
- gem install bundler
- curl -sSL https://sh.rustup.rs | sh -s -- -y --default-toolchain=nightly --profile=minimal
- export PATH="$PATH:$HOME/.cargo/bin"
@@ -28,9 +24,9 @@ before_install:
- sudo apt-get update -qq
- sudo apt-get install qt59base qt59websockets libgl1-mesa-dev
- source /opt/qt59/bin/qt59-env.sh
-
-script:
+ - chmod +x res/libsodium/buildlibsodium.sh
+script:
- qmake -v
- clang++ -v
- g++-5 -v
@@ -40,4 +36,3 @@ script:
- qmake silentdragon-lite.pro CONFIG+=release -spec linux-g++
- res/libsodium/buildlibsodium.sh
- make CC=gcc-5 CXX=g++-5 -j2
-
diff --git a/README.md b/README.md
index 31d4041..aadbe50 100644
--- a/README.md
+++ b/README.md
@@ -3,7 +3,7 @@
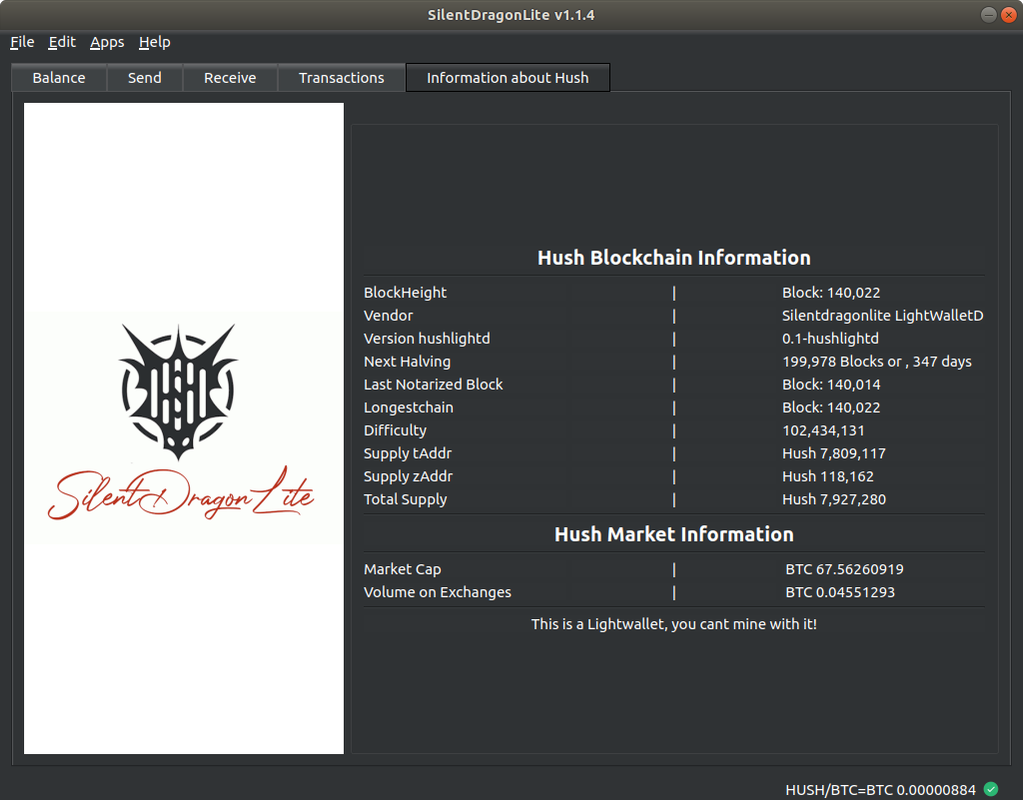
SilentDragonLite is a lightwallet for HUSH ($HUSH) runs on Linux and Windows which does not require you to download the full blockchain. This is experimental software under active development!
-[](https://postimg.cc/21Y0B1vR)
+ ## PRIVACY NOTICE
@@ -15,7 +15,17 @@ This means your IP address is known to these servers. Enable Tor setting in Sile
Go to the releases page and grab the latest installers or binary. https://github.com/MyHush/SilentDragonLite/releases
-### Note Management
+## Install Torsocks (or any other Socks service for TOR) on Ubuntu 18.04
+```
+sudo apt update
+sudo apt install torsocks
+```
+## Connection to our TOR onion service Server
+```
+* Open SDL Edit->Settings->LightwalletServer->rnhk4pwlsbaqzx7wcqfy47lijf2opklstaukq35reiz5rn76crfqpjqd.onion:9067
+* Open the folder of SDL in a Terminal -> Enter: TORSOCKS_LOG_LEVEL=1 torsocks -i ./SilentDragonLite
+```
+## Note Management
SilentDragonLite does automatic note and utxo management, which means it doesn't allow you to manually select which address to send outgoing transactions from. It follows these principles:
* Defaults to sending shielded transactions, even if you're sending to a transparent address
* Sapling funds need at least 2 confirmations before they can be spent
diff --git a/compile.log b/compile.log
deleted file mode 100644
index 6c6584f..0000000
--- a/compile.log
+++ /dev/null
@@ -1,5 +0,0 @@
-Compiling SilentDragonLite 1.2.2 with 4 threads...
-g++ -c -include bin/SilentDragonLite -pipe -g -std=gnu++1y -Wall -W -D_REENTRANT -fPIC -DQT_DEPRECATED_WARNINGS -DQAPPLICATION_CLASS=QApplication -D_FORTIFY_SOURCE=2 -DQT_WIDGETS_LIB -DQT_GUI_LIB -DQT_WEBSOCKETS_LIB -DQT_NETWORK_LIB -DQT_CORE_LIB -I. -Isrc/3rdparty -Isrc -Isingleapplication -Ires -isystem /usr/include/x86_64-linux-gnu/qt5 -isystem /usr/include/x86_64-linux-gnu/qt5/QtWidgets -isystem /usr/include/x86_64-linux-gnu/qt5/QtGui -isystem /usr/include/x86_64-linux-gnu/qt5/QtWebSockets -isystem /usr/include/x86_64-linux-gnu/qt5/QtNetwork -isystem /usr/include/x86_64-linux-gnu/qt5/QtCore -Ibin -Isrc -I/usr/lib/x86_64-linux-gnu/qt5/mkspecs/linux-g++ -o bin/mainwindow.o src/mainwindow.cpp
-g++ -c -include bin/SilentDragonLite -pipe -g -std=gnu++1y -Wall -W -D_REENTRANT -fPIC -DQT_DEPRECATED_WARNINGS -DQAPPLICATION_CLASS=QApplication -D_FORTIFY_SOURCE=2 -DQT_WIDGETS_LIB -DQT_GUI_LIB -DQT_WEBSOCKETS_LIB -DQT_NETWORK_LIB -DQT_CORE_LIB -I. -Isrc/3rdparty -Isrc -Isingleapplication -Ires -isystem /usr/include/x86_64-linux-gnu/qt5 -isystem /usr/include/x86_64-linux-gnu/qt5/QtWidgets -isystem /usr/include/x86_64-linux-gnu/qt5/QtGui -isystem /usr/include/x86_64-linux-gnu/qt5/QtWebSockets -isystem /usr/include/x86_64-linux-gnu/qt5/QtNetwork -isystem /usr/include/x86_64-linux-gnu/qt5/QtCore -Ibin -Isrc -I/usr/lib/x86_64-linux-gnu/qt5/mkspecs/linux-g++ -o bin/sendtab.o src/sendtab.cpp
-g++ -c -include bin/SilentDragonLite -pipe -g -std=gnu++1y -Wall -W -D_REENTRANT -fPIC -DQT_DEPRECATED_WARNINGS -DQAPPLICATION_CLASS=QApplication -D_FORTIFY_SOURCE=2 -DQT_WIDGETS_LIB -DQT_GUI_LIB -DQT_WEBSOCKETS_LIB -DQT_NETWORK_LIB -DQT_CORE_LIB -I. -Isrc/3rdparty -Isrc -Isingleapplication -Ires -isystem /usr/include/x86_64-linux-gnu/qt5 -isystem /usr/include/x86_64-linux-gnu/qt5/QtWidgets -isystem /usr/include/x86_64-linux-gnu/qt5/QtGui -isystem /usr/include/x86_64-linux-gnu/qt5/QtWebSockets -isystem /usr/include/x86_64-linux-gnu/qt5/QtNetwork -isystem /usr/include/x86_64-linux-gnu/qt5/QtCore -Ibin -Isrc -I/usr/lib/x86_64-linux-gnu/qt5/mkspecs/linux-g++ -o bin/addressbook.o src/addressbook.cpp
-g++ -c -include bin/SilentDragonLite -pipe -g -std=gnu++1y -Wall -W -D_REENTRANT -fPIC -DQT_DEPRECATED_WARNINGS -DQAPPLICATION_CLASS=QApplication -D_FORTIFY_SOURCE=2 -DQT_WIDGETS_LIB -DQT_GUI_LIB -DQT_WEBSOCKETS_LIB -DQT_NETWORK_LIB -DQT_CORE_LIB -I. -Isrc/3rdparty -Isrc -Isingleapplication -Ires -isystem /usr/include/x86_64-linux-gnu/qt5 -isystem /usr/include/x86_64-linux-gnu/qt5/QtWidgets -isystem /usr/include/x86_64-linux-gnu/qt5/QtGui -isystem /usr/include/x86_64-linux-gnu/qt5/QtWebSockets -isystem /usr/include/x86_64-linux-gnu/qt5/QtNetwork -isystem /usr/include/x86_64-linux-gnu/qt5/QtCore -Ibin -Isrc -I/usr/lib/x86_64-linux-gnu/qt5/mkspecs/linux-g++ -o bin/addresscombo.o src/addresscombo.cpp
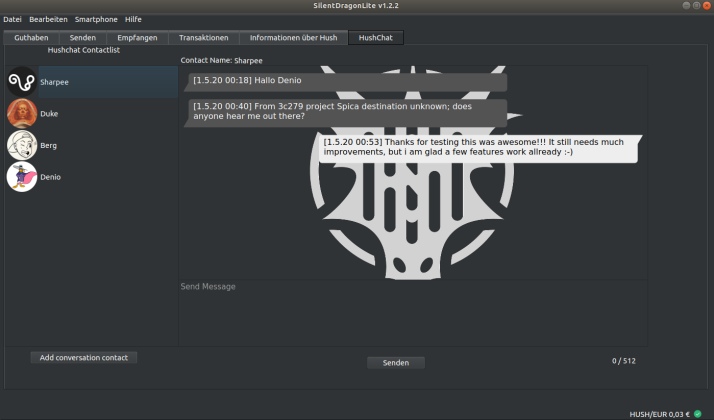
diff --git a/hushchat-screenshot.png b/hushchat-screenshot.png
new file mode 100644
index 0000000..061271d
Binary files /dev/null and b/hushchat-screenshot.png differ
diff --git a/lib/Cargo.lock b/lib/Cargo.lock
index 3c5dbf4..baf8931 100644
--- a/lib/Cargo.lock
+++ b/lib/Cargo.lock
@@ -194,6 +194,20 @@ dependencies = [
"constant_time_eq 0.1.5 (registry+https://github.com/rust-lang/crates.io-index)",
]
+[[package]]
+name = "blake3"
+version = "0.3.4"
+source = "registry+https://github.com/rust-lang/crates.io-index"
+dependencies = [
+ "arrayref 0.3.6 (registry+https://github.com/rust-lang/crates.io-index)",
+ "arrayvec 0.5.1 (registry+https://github.com/rust-lang/crates.io-index)",
+ "cc 1.0.50 (registry+https://github.com/rust-lang/crates.io-index)",
+ "cfg-if 0.1.10 (registry+https://github.com/rust-lang/crates.io-index)",
+ "constant_time_eq 0.1.5 (registry+https://github.com/rust-lang/crates.io-index)",
+ "crypto-mac 0.7.0 (registry+https://github.com/rust-lang/crates.io-index)",
+ "digest 0.8.1 (registry+https://github.com/rust-lang/crates.io-index)",
+]
+
[[package]]
name = "block-buffer"
version = "0.7.3"
@@ -1175,6 +1189,7 @@ dependencies = [
name = "qtlib"
version = "0.1.0"
dependencies = [
+ "blake3 0.3.4 (registry+https://github.com/rust-lang/crates.io-index)",
"lazy_static 1.4.0 (registry+https://github.com/rust-lang/crates.io-index)",
"libc 0.2.66 (registry+https://github.com/rust-lang/crates.io-index)",
"silentdragonlitelib 0.1.0 (git+https://github.com/MyHush/silentdragonlite-cli?rev=d2887d07879a93bdd9b2c8bd12504bb977e82fe0)",
@@ -2461,6 +2476,7 @@ dependencies = [
"checksum bitflags 1.2.1 (registry+https://github.com/rust-lang/crates.io-index)" = "cf1de2fe8c75bc145a2f577add951f8134889b4795d47466a54a5c846d691693"
"checksum blake2b_simd 0.5.10 (registry+https://github.com/rust-lang/crates.io-index)" = "d8fb2d74254a3a0b5cac33ac9f8ed0e44aa50378d9dbb2e5d83bd21ed1dc2c8a"
"checksum blake2s_simd 0.5.10 (registry+https://github.com/rust-lang/crates.io-index)" = "ab9e07352b829279624ceb7c64adb4f585dacdb81d35cafae81139ccd617cf44"
+"checksum blake3 0.3.4 (registry+https://github.com/rust-lang/crates.io-index)" = "423897d97e11b810c9da22458400b28ec866991c711409073662eb34dc44bfff"
"checksum block-buffer 0.7.3 (registry+https://github.com/rust-lang/crates.io-index)" = "c0940dc441f31689269e10ac70eb1002a3a1d3ad1390e030043662eb7fe4688b"
"checksum block-cipher-trait 0.6.2 (registry+https://github.com/rust-lang/crates.io-index)" = "1c924d49bd09e7c06003acda26cd9742e796e34282ec6c1189404dee0c1f4774"
"checksum block-padding 0.1.5 (registry+https://github.com/rust-lang/crates.io-index)" = "fa79dedbb091f449f1f39e53edf88d5dbe95f895dae6135a8d7b881fb5af73f5"
diff --git a/lib/Cargo.toml b/lib/Cargo.toml
index 39a70e9..a0e526e 100644
--- a/lib/Cargo.toml
+++ b/lib/Cargo.toml
@@ -11,4 +11,5 @@ crate-type = ["staticlib"]
[dependencies]
libc = "0.2.58"
lazy_static = "1.4.0"
+blake3 = "0.3.4"
silentdragonlitelib = { git = "https://github.com/MyHush/silentdragonlite-cli", rev = "d2887d07879a93bdd9b2c8bd12504bb977e82fe0" }
diff --git a/lib/silentdragonlitelib.h b/lib/silentdragonlitelib.h
index 4546e70..fdea5db 100644
--- a/lib/silentdragonlitelib.h
+++ b/lib/silentdragonlitelib.h
@@ -13,6 +13,7 @@ extern char * litelib_initialize_new_from_phrase
extern char * litelib_initialize_existing (bool dangerous, const char* server);
extern char * litelib_execute (const char* s, const char* args);
extern void litelib_rust_free_string (char* s);
+extern char * blake3_PW (char* pw);
#ifdef __cplusplus
}
diff --git a/lib/src/lib.rs b/lib/src/lib.rs
index 8be7c55..4ac3bf0 100644
--- a/lib/src/lib.rs
+++ b/lib/src/lib.rs
@@ -29,6 +29,30 @@ pub extern fn litelib_wallet_exists(chain_name: *const c_char) -> bool {
println!("Wallet exists: {}", config.wallet_exists());
config.wallet_exists()
+}
+
+//////hash blake3
+
+#[no_mangle]
+pub extern fn blake3_PW(pw: *const c_char) -> *mut c_char{
+
+ let passwd = unsafe {
+ assert!(!pw.is_null());
+
+ CStr::from_ptr(pw).to_string_lossy().into_owned()
+ };
+
+ let data = passwd.as_bytes();
+// Hash an input all at once.
+let hash1 = blake3::hash(data).to_hex();
+println!("\nBlake3 Hash: {}", hash1);
+
+//let sttring = CString::new(hash1).unwrap();
+let e_str = CString::new(format!("{}", hash1)).unwrap();
+return e_str.into_raw();
+
+
+
}
/// Create a new wallet and return the seed for the newly created wallet.
diff --git a/src/chatmodel.cpp b/src/chatmodel.cpp
index a563398..0b26b3a 100644
--- a/src/chatmodel.cpp
+++ b/src/chatmodel.cpp
@@ -443,43 +443,29 @@ Tx MainWindow::createTxFromChatPage() {
int lengthmemo = memoplain.length();
char *memoplainchar = NULL;
- memoplainchar = new char[lengthmemo+1];
- strncpy(memoplainchar, memoplain.toLocal8Bit(), lengthmemo +1);
-
- /////////We convert the CID from QString to unsigned char*, so we can encrypt it later
- int lengthcid = cid.length();
-
- char *cidchar = NULL;
- cidchar = new char[lengthcid+1];
- strncpy(cidchar, cid.toLocal8Bit(), lengthcid +1);
-
-
-
- QString pubkey = this->getPubkeyByAddress(addr);
- QString passphrase = DataStore::getChatDataStore()->getPassword();
- QString hashEncryptionKey = passphrase;
- int length = hashEncryptionKey.length();
+ memoplainchar = new char[lengthmemo+2];
+ strncpy(memoplainchar, memoplain.toUtf8(), lengthmemo +1);
+ QString pubkey = this->getPubkeyByAddress(addr);
+ QString passphraseHash = DataStore::getChatDataStore()->getPassword();
+ int length = passphraseHash.length();
////////////////Generate the secretkey for our message encryption
- char *hashEncryptionKeyraw = NULL;
- hashEncryptionKeyraw = new char[length+1];
- strncpy(hashEncryptionKeyraw, hashEncryptionKey.toLocal8Bit(), length +1);
+ char *hashEncryptionKeyraw = NULL;
+ hashEncryptionKeyraw = new char[length+1];
+ strncpy(hashEncryptionKeyraw, passphraseHash.toUtf8(), length+1);
#define MESSAGEAS1 ((const unsigned char *) hashEncryptionKeyraw)
#define MESSAGEAS1_LEN length
- unsigned char hash[crypto_kx_SEEDBYTES];
-
- crypto_hash_sha256(hash,MESSAGEAS1, MESSAGEAS1_LEN);
-
+
unsigned char sk[crypto_kx_SECRETKEYBYTES];
unsigned char pk[crypto_kx_PUBLICKEYBYTES];
unsigned char server_rx[crypto_kx_SESSIONKEYBYTES], server_tx[crypto_kx_SESSIONKEYBYTES];
if (crypto_kx_seed_keypair(pk,sk,
- hash) !=0) {
+ MESSAGEAS1) !=0) {
}
////////////////Get the pubkey from Bob, so we can create the share key
@@ -772,29 +758,22 @@ Tx MainWindow::createTxForSafeContactRequest()
QString memo = contactRequest.getMemo();
- // QString privkey = rpc->fetchPrivKey(myAddr);
QString passphrase = DataStore::getChatDataStore()->getPassword();
- QString hashEncryptionKey = passphrase;
- int length = hashEncryptionKey.length();
+ int length = passphrase.length();
////////////////Generate the secretkey for our message encryption
- char *hashEncryptionKeyraw = NULL;
- hashEncryptionKeyraw = new char[length+1];
- strncpy(hashEncryptionKeyraw, hashEncryptionKey.toLocal8Bit(), length +1);
+ char *hashEncryptionKeyraw = NULL;
+ hashEncryptionKeyraw = new char[length+1];
+ strncpy(hashEncryptionKeyraw, passphrase.toUtf8(), length +1);
+
#define MESSAGEAS1 ((const unsigned char *) hashEncryptionKeyraw)
#define MESSAGEAS1_LEN length
-
- unsigned char hash[crypto_kx_SEEDBYTES];
-
- crypto_hash_sha256(hash,MESSAGEAS1, MESSAGEAS1_LEN);
-
-
unsigned char sk[crypto_kx_SECRETKEYBYTES];
unsigned char pk[crypto_kx_PUBLICKEYBYTES];
if (crypto_kx_seed_keypair(pk,sk,
- hash) !=0) {
+ MESSAGEAS1) !=0) {
}
QString publicKey = QByteArray(reinterpret_cast(pk), crypto_kx_PUBLICKEYBYTES).toHex();
diff --git a/src/controller.cpp b/src/controller.cpp
index 7ce4c2d..6dfda83 100644
--- a/src/controller.cpp
+++ b/src/controller.cpp
@@ -1026,32 +1026,25 @@ void Controller::refreshTransactions() {
{
QString passphrase = DataStore::getChatDataStore()->getPassword();
- QString hashEncryptionKey = passphrase;
- int length = hashEncryptionKey.length();
+ int length = passphrase.length();
////////////////Generate the secretkey for our message encryption
char *hashEncryptionKeyraw = NULL;
hashEncryptionKeyraw = new char[length+1];
- strncpy(hashEncryptionKeyraw, hashEncryptionKey.toLocal8Bit(), length +1);
+ strncpy(hashEncryptionKeyraw, passphrase.toUtf8(), length +1);
+
const QByteArray pubkeyBobArray = QByteArray::fromHex(publickey.toLatin1());
const unsigned char *pubkeyBob = reinterpret_cast(pubkeyBobArray.constData());
-
-
-
#define MESSAGEAS1 ((const unsigned char *) hashEncryptionKeyraw)///////////
- #define MESSAGEAS1_LEN length
+ #define MESSAGEAS1_LEN length
-
- unsigned char hash1[crypto_kx_SEEDBYTES];
-
- crypto_hash_sha256(hash1,MESSAGEAS1, MESSAGEAS1_LEN);
unsigned char sk[crypto_kx_SECRETKEYBYTES];
unsigned char pk[crypto_kx_PUBLICKEYBYTES];
if (crypto_kx_seed_keypair(pk,sk,
- hash1) !=0) {
+ MESSAGEAS1) !=0) {
}
unsigned char server_rx[crypto_kx_SESSIONKEYBYTES], server_tx[crypto_kx_SESSIONKEYBYTES];
@@ -1068,7 +1061,7 @@ void Controller::refreshTransactions() {
}
- const QByteArray ba = QByteArray::fromHex(memo.toLatin1());
+ const QByteArray ba = QByteArray::fromHex(memo.toUtf8());
const unsigned char *encryptedMemo = reinterpret_cast(ba.constData());
const QByteArray ba1 = QByteArray::fromHex(headerbytes.toLatin1());
@@ -1292,32 +1285,24 @@ void Controller::refreshTransactions() {
}else{}
QString passphrase = DataStore::getChatDataStore()->getPassword();
- QString hashEncryptionKey = passphrase;
- int length = hashEncryptionKey.length();
+ int length = passphrase.length();
char *hashEncryptionKeyraw = NULL;
hashEncryptionKeyraw = new char[length+1];
- strncpy(hashEncryptionKeyraw, hashEncryptionKey.toLocal8Bit(), length +1);
-
- //const QByteArray ba2 = QByteArray::fromHex(hashEncryptionKey.toLatin1());
- // const unsigned char *hashEncryptionKeyraw = reinterpret_cast(ba2.constData());
+ strncpy(hashEncryptionKeyraw, passphrase.toUtf8(), length +1);
const QByteArray pubkeyBobArray = QByteArray::fromHex(publickey.toLatin1());
const unsigned char *pubkeyBob = reinterpret_cast(pubkeyBobArray.constData());
- #define MESSAGEAS1 ((const unsigned char *) hashEncryptionKeyraw)///////////
- #define MESSAGEAS1_LEN length
+ #define MESSAGEAS1 ((const unsigned char *) hashEncryptionKeyraw)///////////
+ #define MESSAGEAS1_LEN length
-
- unsigned char hash1[crypto_kx_SEEDBYTES];
-
- crypto_hash_sha256(hash1,MESSAGEAS1, MESSAGEAS1_LEN);
- unsigned char sk[crypto_kx_SECRETKEYBYTES];
- unsigned char pk[crypto_kx_PUBLICKEYBYTES];
+ unsigned char sk[crypto_kx_SECRETKEYBYTES];
+ unsigned char pk[crypto_kx_PUBLICKEYBYTES];
if (crypto_kx_seed_keypair(pk,sk,
- hash1) !=0) {
+ MESSAGEAS1) !=0) {
}
@@ -1336,7 +1321,7 @@ void Controller::refreshTransactions() {
- const QByteArray ba = QByteArray::fromHex(memo.toLatin1());
+ const QByteArray ba = QByteArray::fromHex(memo.toUtf8());
const unsigned char *encryptedMemo = reinterpret_cast(ba.constData());
const QByteArray ba1 = QByteArray::fromHex(headerbytes.toLatin1());
@@ -1356,7 +1341,7 @@ void Controller::refreshTransactions() {
//////Set the length of the decrypted message
- unsigned char decrypted[MESSAGE1_LEN];
+ unsigned char decrypted[MESSAGE1_LEN+1];
unsigned char tag[crypto_secretstream_xchacha20poly1305_TAG_FINAL];
crypto_secretstream_xchacha20poly1305_state state;
diff --git a/src/firsttimewizard.cpp b/src/firsttimewizard.cpp
index ca22f4f..f3f3348 100644
--- a/src/firsttimewizard.cpp
+++ b/src/firsttimewizard.cpp
@@ -61,10 +61,13 @@ NewOrRestorePage::NewOrRestorePage(FirstTimeWizard *parent) : QWizardPage(parent
auto fnPasswordEdited = [=](const QString&) {
// Enable the Finish button if the passwords match.
- QString Password = form.txtPassword->text();
+ QString passphraseBlank = form.txtPassword->text();
+
+ QString passphrase = QString("HUSH3") + passphraseBlank + QString("SDL");
+
if (!form.txtPassword->text().isEmpty() &&
- form.txtPassword->text() == form.txtConfirmPassword->text() && Password.size() >= 16) {
+ form.txtPassword->text() == form.txtConfirmPassword->text() && passphraseBlank.size() >= 16) {
form.lblPasswordMatch->setText("");
parent->button(QWizard::CommitButton)->setEnabled(true);
@@ -73,8 +76,36 @@ NewOrRestorePage::NewOrRestorePage(FirstTimeWizard *parent) : QWizardPage(parent
form.radioNewWallet->setEnabled(true);
form.radioNewWallet->setChecked(true);
-
-DataStore::getChatDataStore()->setPassword(Password);
+ int length = passphrase.length();
+
+ char *sequence = NULL;
+ sequence = new char[length+1];
+ strncpy(sequence, passphrase.toUtf8(), length +1);
+
+ QString passphraseHash = blake3_PW(sequence);
+
+
+ char *sequence1 = NULL;
+ sequence1 = new char[length+1];
+ strncpy(sequence1, passphraseHash.toUtf8(), length+1);
+
+ #define MESSAGE ((const unsigned char *) sequence)
+ #define MESSAGE_LEN length
+ #define hash ((const unsigned char *) sequence1)
+
+ #define PASSWORD sequence
+ #define KEY_LEN crypto_box_SEEDBYTES
+
+ unsigned char key[KEY_LEN];
+
+ if (crypto_pwhash
+ (key, sizeof key, PASSWORD, strlen(PASSWORD), hash,
+ crypto_pwhash_OPSLIMIT_SENSITIVE, crypto_pwhash_MEMLIMIT_SENSITIVE,
+ crypto_pwhash_ALG_DEFAULT) != 0) {
+ /* out of memory */
+}
+ QString passphraseHash1 = QByteArray(reinterpret_cast(key), KEY_LEN).toHex();
+ DataStore::getChatDataStore()->setPassword(passphraseHash1);
//main->setPassword(Password);
//qDebug()<<"Objekt gesetzt";
diff --git a/src/mainwindow.cpp b/src/mainwindow.cpp
index e54e9c1..969a575 100644
--- a/src/mainwindow.cpp
+++ b/src/mainwindow.cpp
@@ -33,6 +33,7 @@
#include "Crypto/FileEncryption.h"
#include "DataStore/DataStore.h"
#include "firsttimewizard.h"
+#include "../lib/silentdragonlitelib.h"
using json = nlohmann::json;
@@ -305,53 +306,31 @@ void MainWindow::closeEvent(QCloseEvent* event) {
fileoldencryption.remove();
// Encrypt our wallet.dat
- QString str = DataStore::getChatDataStore()->getPassword();
- // QString str = ed.txtPassword->text(); // data comes from user inputs
- int length = str.length();
+ QString passphraseHash = DataStore::getChatDataStore()->getPassword();
+ int length = passphraseHash.length();
- char *sequence = NULL;
- sequence = new char[length+1];
- strncpy(sequence, str.toLocal8Bit(), length +1);
+ char *sequence1 = NULL;
+ sequence1 = new char[length+1];
+ strncpy(sequence1, passphraseHash.toUtf8(), length+1);
- #define MESSAGE ((const unsigned char *) sequence)
- #define MESSAGE_LEN length
+ #define PassphraseHashEnd ((const unsigned char *) sequence1)
+ #define MESSAGE_LEN length
- unsigned char hash[crypto_secretstream_xchacha20poly1305_KEYBYTES];
+ #define PASSWORD sequence
+ #define KEY_LEN crypto_box_SEEDBYTES
- crypto_hash_sha256(hash,MESSAGE, MESSAGE_LEN);
-
- #define PASSWORD sequence
- #define KEY_LEN crypto_box_SEEDBYTES
-
-
-
- /////////we use the Hash of the Password as Salt, not perfect but still a good solution.
-
- unsigned char key[KEY_LEN];
-
- if (crypto_pwhash
- (key, sizeof key, PASSWORD, strlen(PASSWORD), hash,
- crypto_pwhash_OPSLIMIT_SENSITIVE, crypto_pwhash_MEMLIMIT_SENSITIVE,
- crypto_pwhash_ALG_DEFAULT) != 0) {
- /* out of memory */
-}
-
+ const QByteArray ba = QByteArray::fromHex(passphraseHash.toLatin1());
+ const unsigned char *encryptedMemo1 = reinterpret_cast(ba.constData());
+
auto dir = QDir(QStandardPaths::writableLocation(QStandardPaths::AppDataLocation));
- // auto dirHome = QDir(QStandardPaths::writableLocation(QStandardPaths::HomeLocation));
- // QString source_file = dir.filePath("addresslabels.dat");
- // QString target_enc_file = dir.filePath("addresslabels.dat.enc");
QString sourceWallet_file = dirwallet;
QString target_encWallet_file = dirwalletenc;
// FileEncryption::encrypt(target_enc_file, source_file, key);
- FileEncryption::encrypt(target_encWallet_file, sourceWallet_file, key);
-
- ///////////////// we rename the plaintext wallet.dat to Backup, for testing.
+ FileEncryption::encrypt(target_encWallet_file, sourceWallet_file, encryptedMemo1);
QFile wallet(dirwallet);
- // QFile address(dir.filePath("addresslabels.dat"));
wallet.remove();
- //address.remove();
}
@@ -399,51 +378,49 @@ void MainWindow::encryptWallet() {
if (d.exec() == QDialog::Accepted)
{
- QString passphrase = ed.txtPassword->text(); // data comes from user inputs
+ QString passphraseBlank = ed.txtPassword->text(); // data comes from user inputs
+ QString passphrase = QString("HUSH3") + passphraseBlank + QString("SDL");
int length = passphrase.length();
- DataStore::getChatDataStore()->setPassword(passphrase);
+
- char *sequence = NULL;
- sequence = new char[length+1];
- strncpy(sequence, passphrase.toLocal8Bit(), length +1);
+ char *sequence = NULL;
+ sequence = new char[length+1];
+ strncpy(sequence, passphrase.toUtf8(), length +1);
+
+ QString passphraseHash = blake3_PW(sequence);
+ DataStore::getChatDataStore()->setPassword(passphraseHash);
- #define MESSAGE ((const unsigned char *) sequence)
- #define MESSAGE_LEN length
+ char *sequence1 = NULL;
+ sequence1 = new char[length+1];
+ strncpy(sequence1, passphraseHash.toUtf8(), length+1);
- unsigned char hash[crypto_secretstream_xchacha20poly1305_KEYBYTES];
+ #define MESSAGE ((const unsigned char *) sequence)
+ #define MESSAGE_LEN length
+ #define hash ((const unsigned char *) sequence1)
- crypto_hash_sha256(hash,MESSAGE, MESSAGE_LEN);
+ #define PASSWORD sequence
+ #define KEY_LEN crypto_box_SEEDBYTES
- #define PASSWORD sequence
- #define KEY_LEN crypto_box_SEEDBYTES
+ unsigned char key[KEY_LEN];
-
-
- /////////we use the Hash of the Password as Salt, not perfect but still a good solution.
-
- unsigned char key[KEY_LEN];
-
- if (crypto_pwhash
- (key, sizeof key, PASSWORD, strlen(PASSWORD), hash,
- crypto_pwhash_OPSLIMIT_SENSITIVE, crypto_pwhash_MEMLIMIT_SENSITIVE,
- crypto_pwhash_ALG_DEFAULT) != 0) {
- /* out of memory */
+ if (crypto_pwhash
+ (key, sizeof key, PASSWORD, strlen(PASSWORD), hash,
+ crypto_pwhash_OPSLIMIT_SENSITIVE, crypto_pwhash_MEMLIMIT_SENSITIVE,
+ crypto_pwhash_ALG_DEFAULT) != 0) {
+ /* out of memory */
}
+ QString passphraseHash1 = QByteArray(reinterpret_cast(key), KEY_LEN).toHex();
+ DataStore::getChatDataStore()->setPassword(passphraseHash1);
auto dir = QDir(QStandardPaths::writableLocation(QStandardPaths::AppDataLocation));
auto dirHome = QDir(QStandardPaths::writableLocation(QStandardPaths::HomeLocation));
- // QString source_file = dir.filePath("addresslabels.dat");
- // QString target_enc_file = dir.filePath("addresslabels.dat.enc");
QString sourceWallet_file = dirwallet;
QString target_encWallet_file = dirwalletenc;
-
- // FileEncryption::encrypt(target_enc_file, source_file, key);
+
FileEncryption::encrypt(target_encWallet_file, sourceWallet_file, key);
QFile wallet(dirwallet);
- // QFile address(dir.filePath("addresslabels.dat"));
wallet.rename(dirwalletbackup);
- // address.rename(dir.filePath("addresslabels.datBackup"));
QMessageBox::information(this, tr("Wallet Encryption Success"),
QString("Successfully encrypted your wallet"),
@@ -484,27 +461,28 @@ void MainWindow::removeWalletEncryption() {
if (d.exec() == QDialog::Accepted)
{
- QString str = ed.txtPassword->text(); // data comes from user inputs
- int length = str.length();
+ QString passphraseBlank = ed.txtPassword->text(); // data comes from user inputs
+
+ QString passphrase = QString("HUSH3") + passphraseBlank + QString("SDL");
+
+ int length = passphrase.length();
char *sequence = NULL;
sequence = new char[length+1];
- strncpy(sequence, str.toLocal8Bit(), length +1);
+ strncpy(sequence, passphrase.toUtf8(), length +1);
- #define MESSAGE ((const unsigned char *) sequence)
- #define MESSAGE_LEN length
+ QString passphraseHash = blake3_PW(sequence);
- unsigned char hash[crypto_secretstream_xchacha20poly1305_KEYBYTES];
+ char *sequence1 = NULL;
+ sequence1 = new char[length+1];
+ strncpy(sequence1, passphraseHash.toUtf8(), length+1);
- crypto_hash_sha256(hash,MESSAGE, MESSAGE_LEN);
+
+ #define hash ((const unsigned char *) sequence1)
#define PASSWORD sequence
#define KEY_LEN crypto_box_SEEDBYTES
-
-
- /////////we use the Hash of the Password as Salt, not perfect but still a good solution.
-
unsigned char key[KEY_LEN];
if (crypto_pwhash
@@ -513,18 +491,14 @@ void MainWindow::removeWalletEncryption() {
crypto_pwhash_ALG_DEFAULT) != 0) {
/* out of memory */
}
-
-
auto dir = QDir(QStandardPaths::writableLocation(QStandardPaths::AppDataLocation));
auto dirHome = QDir(QStandardPaths::writableLocation(QStandardPaths::HomeLocation));
QString target_encwallet_file = dirwalletenc;
QString target_decwallet_file = dirwallet;
- // QString target_encaddr_file = dir.filePath("addresslabels.dat.enc");
- // QString target_decaddr_file = dir.filePath("addresslabels.dat");
FileEncryption::decrypt(target_decwallet_file, target_encwallet_file, key);
- // FileEncryption::decrypt(target_decaddr_file, target_encaddr_file, key);
+
QFile filencrypted(dirwalletenc);
QFile wallet(dirwallet);
@@ -556,56 +530,54 @@ void MainWindow::removeWalletEncryptionStartUp() {
QDialog d(this);
Ui_startup ed;
ed.setupUi(&d);
-
+
if (d.exec() == QDialog::Accepted)
{
- QString password = ed.txtPassword->text(); // data comes from user inputs
- int length = password.length();
- DataStore::getChatDataStore()->setPassword(password);
+ QString passphraseBlank = ed.txtPassword->text(); // data comes from user inputs
+
+ QString passphrase = QString("HUSH3") + passphraseBlank + QString("SDL");
+ int length = passphrase.length();
+
char *sequence = NULL;
sequence = new char[length+1];
- strncpy(sequence, password.toLocal8Bit(), length +1);
+ strncpy(sequence, passphrase.toUtf8(), length +1);
+
+ QString passphraseHash = blake3_PW(sequence);
+
+
+ char *sequence1 = NULL;
+ sequence1 = new char[length+1];
+ strncpy(sequence1, passphraseHash.toUtf8(), length+1);
#define MESSAGE ((const unsigned char *) sequence)
#define MESSAGE_LEN length
-
- unsigned char hash[crypto_secretstream_xchacha20poly1305_KEYBYTES];
-
- crypto_hash_sha256(hash,MESSAGE, MESSAGE_LEN);
+ #define hash ((const unsigned char *) sequence1)
#define PASSWORD sequence
- #define KEY_LEN crypto_box_SEEDBYTES
+ #define KEY_LEN crypto_box_SEEDBYTES
-
+ unsigned char key[KEY_LEN];
- /////////we use the Hash of the Password as Salt, not perfect but still a good solution.
-
- unsigned char key[KEY_LEN];
-
- if (crypto_pwhash
- (key, sizeof key, PASSWORD, strlen(PASSWORD), hash,
- crypto_pwhash_OPSLIMIT_SENSITIVE, crypto_pwhash_MEMLIMIT_SENSITIVE,
- crypto_pwhash_ALG_DEFAULT) != 0) {
+ if (crypto_pwhash
+ (key, sizeof key, PASSWORD, strlen(PASSWORD), hash,
+ crypto_pwhash_OPSLIMIT_SENSITIVE, crypto_pwhash_MEMLIMIT_SENSITIVE,
+ crypto_pwhash_ALG_DEFAULT) != 0) {
/* out of memory */
- }
+}
+ QString passphraseHash1 = QByteArray(reinterpret_cast(key), KEY_LEN).toHex();
+ DataStore::getChatDataStore()->setPassword(passphraseHash1);
-
- {
auto dir = QDir(QStandardPaths::writableLocation(QStandardPaths::AppDataLocation));
- auto dirHome = QDir(QStandardPaths::writableLocation(QStandardPaths::HomeLocation));
+
QString target_encwallet_file = dirwalletenc;
QString target_decwallet_file = dirwallet;
- // QString target_encaddr_file = dir.filePath("addresslabels.dat.enc");
- // QString target_decaddr_file = dir.filePath("addresslabels.dat");
FileEncryption::decrypt(target_decwallet_file, target_encwallet_file, key);
- // FileEncryption::decrypt(target_decaddr_file, target_encaddr_file, key);
- }
+
auto dirHome = QDir(QStandardPaths::writableLocation(QStandardPaths::HomeLocation));
QFile wallet(dirwallet);
- //QFile backup(dirHome.filePath(".silentdragonlite/silentdragonlite-wallet.datBACKUP"));*/
if (wallet.size() > 0)
{
## PRIVACY NOTICE
@@ -15,7 +15,17 @@ This means your IP address is known to these servers. Enable Tor setting in Sile
Go to the releases page and grab the latest installers or binary. https://github.com/MyHush/SilentDragonLite/releases
-### Note Management
+## Install Torsocks (or any other Socks service for TOR) on Ubuntu 18.04
+```
+sudo apt update
+sudo apt install torsocks
+```
+## Connection to our TOR onion service Server
+```
+* Open SDL Edit->Settings->LightwalletServer->rnhk4pwlsbaqzx7wcqfy47lijf2opklstaukq35reiz5rn76crfqpjqd.onion:9067
+* Open the folder of SDL in a Terminal -> Enter: TORSOCKS_LOG_LEVEL=1 torsocks -i ./SilentDragonLite
+```
+## Note Management
SilentDragonLite does automatic note and utxo management, which means it doesn't allow you to manually select which address to send outgoing transactions from. It follows these principles:
* Defaults to sending shielded transactions, even if you're sending to a transparent address
* Sapling funds need at least 2 confirmations before they can be spent
diff --git a/compile.log b/compile.log
deleted file mode 100644
index 6c6584f..0000000
--- a/compile.log
+++ /dev/null
@@ -1,5 +0,0 @@
-Compiling SilentDragonLite 1.2.2 with 4 threads...
-g++ -c -include bin/SilentDragonLite -pipe -g -std=gnu++1y -Wall -W -D_REENTRANT -fPIC -DQT_DEPRECATED_WARNINGS -DQAPPLICATION_CLASS=QApplication -D_FORTIFY_SOURCE=2 -DQT_WIDGETS_LIB -DQT_GUI_LIB -DQT_WEBSOCKETS_LIB -DQT_NETWORK_LIB -DQT_CORE_LIB -I. -Isrc/3rdparty -Isrc -Isingleapplication -Ires -isystem /usr/include/x86_64-linux-gnu/qt5 -isystem /usr/include/x86_64-linux-gnu/qt5/QtWidgets -isystem /usr/include/x86_64-linux-gnu/qt5/QtGui -isystem /usr/include/x86_64-linux-gnu/qt5/QtWebSockets -isystem /usr/include/x86_64-linux-gnu/qt5/QtNetwork -isystem /usr/include/x86_64-linux-gnu/qt5/QtCore -Ibin -Isrc -I/usr/lib/x86_64-linux-gnu/qt5/mkspecs/linux-g++ -o bin/mainwindow.o src/mainwindow.cpp
-g++ -c -include bin/SilentDragonLite -pipe -g -std=gnu++1y -Wall -W -D_REENTRANT -fPIC -DQT_DEPRECATED_WARNINGS -DQAPPLICATION_CLASS=QApplication -D_FORTIFY_SOURCE=2 -DQT_WIDGETS_LIB -DQT_GUI_LIB -DQT_WEBSOCKETS_LIB -DQT_NETWORK_LIB -DQT_CORE_LIB -I. -Isrc/3rdparty -Isrc -Isingleapplication -Ires -isystem /usr/include/x86_64-linux-gnu/qt5 -isystem /usr/include/x86_64-linux-gnu/qt5/QtWidgets -isystem /usr/include/x86_64-linux-gnu/qt5/QtGui -isystem /usr/include/x86_64-linux-gnu/qt5/QtWebSockets -isystem /usr/include/x86_64-linux-gnu/qt5/QtNetwork -isystem /usr/include/x86_64-linux-gnu/qt5/QtCore -Ibin -Isrc -I/usr/lib/x86_64-linux-gnu/qt5/mkspecs/linux-g++ -o bin/sendtab.o src/sendtab.cpp
-g++ -c -include bin/SilentDragonLite -pipe -g -std=gnu++1y -Wall -W -D_REENTRANT -fPIC -DQT_DEPRECATED_WARNINGS -DQAPPLICATION_CLASS=QApplication -D_FORTIFY_SOURCE=2 -DQT_WIDGETS_LIB -DQT_GUI_LIB -DQT_WEBSOCKETS_LIB -DQT_NETWORK_LIB -DQT_CORE_LIB -I. -Isrc/3rdparty -Isrc -Isingleapplication -Ires -isystem /usr/include/x86_64-linux-gnu/qt5 -isystem /usr/include/x86_64-linux-gnu/qt5/QtWidgets -isystem /usr/include/x86_64-linux-gnu/qt5/QtGui -isystem /usr/include/x86_64-linux-gnu/qt5/QtWebSockets -isystem /usr/include/x86_64-linux-gnu/qt5/QtNetwork -isystem /usr/include/x86_64-linux-gnu/qt5/QtCore -Ibin -Isrc -I/usr/lib/x86_64-linux-gnu/qt5/mkspecs/linux-g++ -o bin/addressbook.o src/addressbook.cpp
-g++ -c -include bin/SilentDragonLite -pipe -g -std=gnu++1y -Wall -W -D_REENTRANT -fPIC -DQT_DEPRECATED_WARNINGS -DQAPPLICATION_CLASS=QApplication -D_FORTIFY_SOURCE=2 -DQT_WIDGETS_LIB -DQT_GUI_LIB -DQT_WEBSOCKETS_LIB -DQT_NETWORK_LIB -DQT_CORE_LIB -I. -Isrc/3rdparty -Isrc -Isingleapplication -Ires -isystem /usr/include/x86_64-linux-gnu/qt5 -isystem /usr/include/x86_64-linux-gnu/qt5/QtWidgets -isystem /usr/include/x86_64-linux-gnu/qt5/QtGui -isystem /usr/include/x86_64-linux-gnu/qt5/QtWebSockets -isystem /usr/include/x86_64-linux-gnu/qt5/QtNetwork -isystem /usr/include/x86_64-linux-gnu/qt5/QtCore -Ibin -Isrc -I/usr/lib/x86_64-linux-gnu/qt5/mkspecs/linux-g++ -o bin/addresscombo.o src/addresscombo.cpp
diff --git a/hushchat-screenshot.png b/hushchat-screenshot.png
new file mode 100644
index 0000000..061271d
Binary files /dev/null and b/hushchat-screenshot.png differ
diff --git a/lib/Cargo.lock b/lib/Cargo.lock
index 3c5dbf4..baf8931 100644
--- a/lib/Cargo.lock
+++ b/lib/Cargo.lock
@@ -194,6 +194,20 @@ dependencies = [
"constant_time_eq 0.1.5 (registry+https://github.com/rust-lang/crates.io-index)",
]
+[[package]]
+name = "blake3"
+version = "0.3.4"
+source = "registry+https://github.com/rust-lang/crates.io-index"
+dependencies = [
+ "arrayref 0.3.6 (registry+https://github.com/rust-lang/crates.io-index)",
+ "arrayvec 0.5.1 (registry+https://github.com/rust-lang/crates.io-index)",
+ "cc 1.0.50 (registry+https://github.com/rust-lang/crates.io-index)",
+ "cfg-if 0.1.10 (registry+https://github.com/rust-lang/crates.io-index)",
+ "constant_time_eq 0.1.5 (registry+https://github.com/rust-lang/crates.io-index)",
+ "crypto-mac 0.7.0 (registry+https://github.com/rust-lang/crates.io-index)",
+ "digest 0.8.1 (registry+https://github.com/rust-lang/crates.io-index)",
+]
+
[[package]]
name = "block-buffer"
version = "0.7.3"
@@ -1175,6 +1189,7 @@ dependencies = [
name = "qtlib"
version = "0.1.0"
dependencies = [
+ "blake3 0.3.4 (registry+https://github.com/rust-lang/crates.io-index)",
"lazy_static 1.4.0 (registry+https://github.com/rust-lang/crates.io-index)",
"libc 0.2.66 (registry+https://github.com/rust-lang/crates.io-index)",
"silentdragonlitelib 0.1.0 (git+https://github.com/MyHush/silentdragonlite-cli?rev=d2887d07879a93bdd9b2c8bd12504bb977e82fe0)",
@@ -2461,6 +2476,7 @@ dependencies = [
"checksum bitflags 1.2.1 (registry+https://github.com/rust-lang/crates.io-index)" = "cf1de2fe8c75bc145a2f577add951f8134889b4795d47466a54a5c846d691693"
"checksum blake2b_simd 0.5.10 (registry+https://github.com/rust-lang/crates.io-index)" = "d8fb2d74254a3a0b5cac33ac9f8ed0e44aa50378d9dbb2e5d83bd21ed1dc2c8a"
"checksum blake2s_simd 0.5.10 (registry+https://github.com/rust-lang/crates.io-index)" = "ab9e07352b829279624ceb7c64adb4f585dacdb81d35cafae81139ccd617cf44"
+"checksum blake3 0.3.4 (registry+https://github.com/rust-lang/crates.io-index)" = "423897d97e11b810c9da22458400b28ec866991c711409073662eb34dc44bfff"
"checksum block-buffer 0.7.3 (registry+https://github.com/rust-lang/crates.io-index)" = "c0940dc441f31689269e10ac70eb1002a3a1d3ad1390e030043662eb7fe4688b"
"checksum block-cipher-trait 0.6.2 (registry+https://github.com/rust-lang/crates.io-index)" = "1c924d49bd09e7c06003acda26cd9742e796e34282ec6c1189404dee0c1f4774"
"checksum block-padding 0.1.5 (registry+https://github.com/rust-lang/crates.io-index)" = "fa79dedbb091f449f1f39e53edf88d5dbe95f895dae6135a8d7b881fb5af73f5"
diff --git a/lib/Cargo.toml b/lib/Cargo.toml
index 39a70e9..a0e526e 100644
--- a/lib/Cargo.toml
+++ b/lib/Cargo.toml
@@ -11,4 +11,5 @@ crate-type = ["staticlib"]
[dependencies]
libc = "0.2.58"
lazy_static = "1.4.0"
+blake3 = "0.3.4"
silentdragonlitelib = { git = "https://github.com/MyHush/silentdragonlite-cli", rev = "d2887d07879a93bdd9b2c8bd12504bb977e82fe0" }
diff --git a/lib/silentdragonlitelib.h b/lib/silentdragonlitelib.h
index 4546e70..fdea5db 100644
--- a/lib/silentdragonlitelib.h
+++ b/lib/silentdragonlitelib.h
@@ -13,6 +13,7 @@ extern char * litelib_initialize_new_from_phrase
extern char * litelib_initialize_existing (bool dangerous, const char* server);
extern char * litelib_execute (const char* s, const char* args);
extern void litelib_rust_free_string (char* s);
+extern char * blake3_PW (char* pw);
#ifdef __cplusplus
}
diff --git a/lib/src/lib.rs b/lib/src/lib.rs
index 8be7c55..4ac3bf0 100644
--- a/lib/src/lib.rs
+++ b/lib/src/lib.rs
@@ -29,6 +29,30 @@ pub extern fn litelib_wallet_exists(chain_name: *const c_char) -> bool {
println!("Wallet exists: {}", config.wallet_exists());
config.wallet_exists()
+}
+
+//////hash blake3
+
+#[no_mangle]
+pub extern fn blake3_PW(pw: *const c_char) -> *mut c_char{
+
+ let passwd = unsafe {
+ assert!(!pw.is_null());
+
+ CStr::from_ptr(pw).to_string_lossy().into_owned()
+ };
+
+ let data = passwd.as_bytes();
+// Hash an input all at once.
+let hash1 = blake3::hash(data).to_hex();
+println!("\nBlake3 Hash: {}", hash1);
+
+//let sttring = CString::new(hash1).unwrap();
+let e_str = CString::new(format!("{}", hash1)).unwrap();
+return e_str.into_raw();
+
+
+
}
/// Create a new wallet and return the seed for the newly created wallet.
diff --git a/src/chatmodel.cpp b/src/chatmodel.cpp
index a563398..0b26b3a 100644
--- a/src/chatmodel.cpp
+++ b/src/chatmodel.cpp
@@ -443,43 +443,29 @@ Tx MainWindow::createTxFromChatPage() {
int lengthmemo = memoplain.length();
char *memoplainchar = NULL;
- memoplainchar = new char[lengthmemo+1];
- strncpy(memoplainchar, memoplain.toLocal8Bit(), lengthmemo +1);
-
- /////////We convert the CID from QString to unsigned char*, so we can encrypt it later
- int lengthcid = cid.length();
-
- char *cidchar = NULL;
- cidchar = new char[lengthcid+1];
- strncpy(cidchar, cid.toLocal8Bit(), lengthcid +1);
-
-
-
- QString pubkey = this->getPubkeyByAddress(addr);
- QString passphrase = DataStore::getChatDataStore()->getPassword();
- QString hashEncryptionKey = passphrase;
- int length = hashEncryptionKey.length();
+ memoplainchar = new char[lengthmemo+2];
+ strncpy(memoplainchar, memoplain.toUtf8(), lengthmemo +1);
+ QString pubkey = this->getPubkeyByAddress(addr);
+ QString passphraseHash = DataStore::getChatDataStore()->getPassword();
+ int length = passphraseHash.length();
////////////////Generate the secretkey for our message encryption
- char *hashEncryptionKeyraw = NULL;
- hashEncryptionKeyraw = new char[length+1];
- strncpy(hashEncryptionKeyraw, hashEncryptionKey.toLocal8Bit(), length +1);
+ char *hashEncryptionKeyraw = NULL;
+ hashEncryptionKeyraw = new char[length+1];
+ strncpy(hashEncryptionKeyraw, passphraseHash.toUtf8(), length+1);
#define MESSAGEAS1 ((const unsigned char *) hashEncryptionKeyraw)
#define MESSAGEAS1_LEN length
- unsigned char hash[crypto_kx_SEEDBYTES];
-
- crypto_hash_sha256(hash,MESSAGEAS1, MESSAGEAS1_LEN);
-
+
unsigned char sk[crypto_kx_SECRETKEYBYTES];
unsigned char pk[crypto_kx_PUBLICKEYBYTES];
unsigned char server_rx[crypto_kx_SESSIONKEYBYTES], server_tx[crypto_kx_SESSIONKEYBYTES];
if (crypto_kx_seed_keypair(pk,sk,
- hash) !=0) {
+ MESSAGEAS1) !=0) {
}
////////////////Get the pubkey from Bob, so we can create the share key
@@ -772,29 +758,22 @@ Tx MainWindow::createTxForSafeContactRequest()
QString memo = contactRequest.getMemo();
- // QString privkey = rpc->fetchPrivKey(myAddr);
QString passphrase = DataStore::getChatDataStore()->getPassword();
- QString hashEncryptionKey = passphrase;
- int length = hashEncryptionKey.length();
+ int length = passphrase.length();
////////////////Generate the secretkey for our message encryption
- char *hashEncryptionKeyraw = NULL;
- hashEncryptionKeyraw = new char[length+1];
- strncpy(hashEncryptionKeyraw, hashEncryptionKey.toLocal8Bit(), length +1);
+ char *hashEncryptionKeyraw = NULL;
+ hashEncryptionKeyraw = new char[length+1];
+ strncpy(hashEncryptionKeyraw, passphrase.toUtf8(), length +1);
+
#define MESSAGEAS1 ((const unsigned char *) hashEncryptionKeyraw)
#define MESSAGEAS1_LEN length
-
- unsigned char hash[crypto_kx_SEEDBYTES];
-
- crypto_hash_sha256(hash,MESSAGEAS1, MESSAGEAS1_LEN);
-
-
unsigned char sk[crypto_kx_SECRETKEYBYTES];
unsigned char pk[crypto_kx_PUBLICKEYBYTES];
if (crypto_kx_seed_keypair(pk,sk,
- hash) !=0) {
+ MESSAGEAS1) !=0) {
}
QString publicKey = QByteArray(reinterpret_cast(pk), crypto_kx_PUBLICKEYBYTES).toHex();
diff --git a/src/controller.cpp b/src/controller.cpp
index 7ce4c2d..6dfda83 100644
--- a/src/controller.cpp
+++ b/src/controller.cpp
@@ -1026,32 +1026,25 @@ void Controller::refreshTransactions() {
{
QString passphrase = DataStore::getChatDataStore()->getPassword();
- QString hashEncryptionKey = passphrase;
- int length = hashEncryptionKey.length();
+ int length = passphrase.length();
////////////////Generate the secretkey for our message encryption
char *hashEncryptionKeyraw = NULL;
hashEncryptionKeyraw = new char[length+1];
- strncpy(hashEncryptionKeyraw, hashEncryptionKey.toLocal8Bit(), length +1);
+ strncpy(hashEncryptionKeyraw, passphrase.toUtf8(), length +1);
+
const QByteArray pubkeyBobArray = QByteArray::fromHex(publickey.toLatin1());
const unsigned char *pubkeyBob = reinterpret_cast(pubkeyBobArray.constData());
-
-
-
#define MESSAGEAS1 ((const unsigned char *) hashEncryptionKeyraw)///////////
- #define MESSAGEAS1_LEN length
+ #define MESSAGEAS1_LEN length
-
- unsigned char hash1[crypto_kx_SEEDBYTES];
-
- crypto_hash_sha256(hash1,MESSAGEAS1, MESSAGEAS1_LEN);
unsigned char sk[crypto_kx_SECRETKEYBYTES];
unsigned char pk[crypto_kx_PUBLICKEYBYTES];
if (crypto_kx_seed_keypair(pk,sk,
- hash1) !=0) {
+ MESSAGEAS1) !=0) {
}
unsigned char server_rx[crypto_kx_SESSIONKEYBYTES], server_tx[crypto_kx_SESSIONKEYBYTES];
@@ -1068,7 +1061,7 @@ void Controller::refreshTransactions() {
}
- const QByteArray ba = QByteArray::fromHex(memo.toLatin1());
+ const QByteArray ba = QByteArray::fromHex(memo.toUtf8());
const unsigned char *encryptedMemo = reinterpret_cast(ba.constData());
const QByteArray ba1 = QByteArray::fromHex(headerbytes.toLatin1());
@@ -1292,32 +1285,24 @@ void Controller::refreshTransactions() {
}else{}
QString passphrase = DataStore::getChatDataStore()->getPassword();
- QString hashEncryptionKey = passphrase;
- int length = hashEncryptionKey.length();
+ int length = passphrase.length();
char *hashEncryptionKeyraw = NULL;
hashEncryptionKeyraw = new char[length+1];
- strncpy(hashEncryptionKeyraw, hashEncryptionKey.toLocal8Bit(), length +1);
-
- //const QByteArray ba2 = QByteArray::fromHex(hashEncryptionKey.toLatin1());
- // const unsigned char *hashEncryptionKeyraw = reinterpret_cast(ba2.constData());
+ strncpy(hashEncryptionKeyraw, passphrase.toUtf8(), length +1);
const QByteArray pubkeyBobArray = QByteArray::fromHex(publickey.toLatin1());
const unsigned char *pubkeyBob = reinterpret_cast(pubkeyBobArray.constData());
- #define MESSAGEAS1 ((const unsigned char *) hashEncryptionKeyraw)///////////
- #define MESSAGEAS1_LEN length
+ #define MESSAGEAS1 ((const unsigned char *) hashEncryptionKeyraw)///////////
+ #define MESSAGEAS1_LEN length
-
- unsigned char hash1[crypto_kx_SEEDBYTES];
-
- crypto_hash_sha256(hash1,MESSAGEAS1, MESSAGEAS1_LEN);
- unsigned char sk[crypto_kx_SECRETKEYBYTES];
- unsigned char pk[crypto_kx_PUBLICKEYBYTES];
+ unsigned char sk[crypto_kx_SECRETKEYBYTES];
+ unsigned char pk[crypto_kx_PUBLICKEYBYTES];
if (crypto_kx_seed_keypair(pk,sk,
- hash1) !=0) {
+ MESSAGEAS1) !=0) {
}
@@ -1336,7 +1321,7 @@ void Controller::refreshTransactions() {
- const QByteArray ba = QByteArray::fromHex(memo.toLatin1());
+ const QByteArray ba = QByteArray::fromHex(memo.toUtf8());
const unsigned char *encryptedMemo = reinterpret_cast(ba.constData());
const QByteArray ba1 = QByteArray::fromHex(headerbytes.toLatin1());
@@ -1356,7 +1341,7 @@ void Controller::refreshTransactions() {
//////Set the length of the decrypted message
- unsigned char decrypted[MESSAGE1_LEN];
+ unsigned char decrypted[MESSAGE1_LEN+1];
unsigned char tag[crypto_secretstream_xchacha20poly1305_TAG_FINAL];
crypto_secretstream_xchacha20poly1305_state state;
diff --git a/src/firsttimewizard.cpp b/src/firsttimewizard.cpp
index ca22f4f..f3f3348 100644
--- a/src/firsttimewizard.cpp
+++ b/src/firsttimewizard.cpp
@@ -61,10 +61,13 @@ NewOrRestorePage::NewOrRestorePage(FirstTimeWizard *parent) : QWizardPage(parent
auto fnPasswordEdited = [=](const QString&) {
// Enable the Finish button if the passwords match.
- QString Password = form.txtPassword->text();
+ QString passphraseBlank = form.txtPassword->text();
+
+ QString passphrase = QString("HUSH3") + passphraseBlank + QString("SDL");
+
if (!form.txtPassword->text().isEmpty() &&
- form.txtPassword->text() == form.txtConfirmPassword->text() && Password.size() >= 16) {
+ form.txtPassword->text() == form.txtConfirmPassword->text() && passphraseBlank.size() >= 16) {
form.lblPasswordMatch->setText("");
parent->button(QWizard::CommitButton)->setEnabled(true);
@@ -73,8 +76,36 @@ NewOrRestorePage::NewOrRestorePage(FirstTimeWizard *parent) : QWizardPage(parent
form.radioNewWallet->setEnabled(true);
form.radioNewWallet->setChecked(true);
-
-DataStore::getChatDataStore()->setPassword(Password);
+ int length = passphrase.length();
+
+ char *sequence = NULL;
+ sequence = new char[length+1];
+ strncpy(sequence, passphrase.toUtf8(), length +1);
+
+ QString passphraseHash = blake3_PW(sequence);
+
+
+ char *sequence1 = NULL;
+ sequence1 = new char[length+1];
+ strncpy(sequence1, passphraseHash.toUtf8(), length+1);
+
+ #define MESSAGE ((const unsigned char *) sequence)
+ #define MESSAGE_LEN length
+ #define hash ((const unsigned char *) sequence1)
+
+ #define PASSWORD sequence
+ #define KEY_LEN crypto_box_SEEDBYTES
+
+ unsigned char key[KEY_LEN];
+
+ if (crypto_pwhash
+ (key, sizeof key, PASSWORD, strlen(PASSWORD), hash,
+ crypto_pwhash_OPSLIMIT_SENSITIVE, crypto_pwhash_MEMLIMIT_SENSITIVE,
+ crypto_pwhash_ALG_DEFAULT) != 0) {
+ /* out of memory */
+}
+ QString passphraseHash1 = QByteArray(reinterpret_cast(key), KEY_LEN).toHex();
+ DataStore::getChatDataStore()->setPassword(passphraseHash1);
//main->setPassword(Password);
//qDebug()<<"Objekt gesetzt";
diff --git a/src/mainwindow.cpp b/src/mainwindow.cpp
index e54e9c1..969a575 100644
--- a/src/mainwindow.cpp
+++ b/src/mainwindow.cpp
@@ -33,6 +33,7 @@
#include "Crypto/FileEncryption.h"
#include "DataStore/DataStore.h"
#include "firsttimewizard.h"
+#include "../lib/silentdragonlitelib.h"
using json = nlohmann::json;
@@ -305,53 +306,31 @@ void MainWindow::closeEvent(QCloseEvent* event) {
fileoldencryption.remove();
// Encrypt our wallet.dat
- QString str = DataStore::getChatDataStore()->getPassword();
- // QString str = ed.txtPassword->text(); // data comes from user inputs
- int length = str.length();
+ QString passphraseHash = DataStore::getChatDataStore()->getPassword();
+ int length = passphraseHash.length();
- char *sequence = NULL;
- sequence = new char[length+1];
- strncpy(sequence, str.toLocal8Bit(), length +1);
+ char *sequence1 = NULL;
+ sequence1 = new char[length+1];
+ strncpy(sequence1, passphraseHash.toUtf8(), length+1);
- #define MESSAGE ((const unsigned char *) sequence)
- #define MESSAGE_LEN length
+ #define PassphraseHashEnd ((const unsigned char *) sequence1)
+ #define MESSAGE_LEN length
- unsigned char hash[crypto_secretstream_xchacha20poly1305_KEYBYTES];
+ #define PASSWORD sequence
+ #define KEY_LEN crypto_box_SEEDBYTES
- crypto_hash_sha256(hash,MESSAGE, MESSAGE_LEN);
-
- #define PASSWORD sequence
- #define KEY_LEN crypto_box_SEEDBYTES
-
-
-
- /////////we use the Hash of the Password as Salt, not perfect but still a good solution.
-
- unsigned char key[KEY_LEN];
-
- if (crypto_pwhash
- (key, sizeof key, PASSWORD, strlen(PASSWORD), hash,
- crypto_pwhash_OPSLIMIT_SENSITIVE, crypto_pwhash_MEMLIMIT_SENSITIVE,
- crypto_pwhash_ALG_DEFAULT) != 0) {
- /* out of memory */
-}
-
+ const QByteArray ba = QByteArray::fromHex(passphraseHash.toLatin1());
+ const unsigned char *encryptedMemo1 = reinterpret_cast(ba.constData());
+
auto dir = QDir(QStandardPaths::writableLocation(QStandardPaths::AppDataLocation));
- // auto dirHome = QDir(QStandardPaths::writableLocation(QStandardPaths::HomeLocation));
- // QString source_file = dir.filePath("addresslabels.dat");
- // QString target_enc_file = dir.filePath("addresslabels.dat.enc");
QString sourceWallet_file = dirwallet;
QString target_encWallet_file = dirwalletenc;
// FileEncryption::encrypt(target_enc_file, source_file, key);
- FileEncryption::encrypt(target_encWallet_file, sourceWallet_file, key);
-
- ///////////////// we rename the plaintext wallet.dat to Backup, for testing.
+ FileEncryption::encrypt(target_encWallet_file, sourceWallet_file, encryptedMemo1);
QFile wallet(dirwallet);
- // QFile address(dir.filePath("addresslabels.dat"));
wallet.remove();
- //address.remove();
}
@@ -399,51 +378,49 @@ void MainWindow::encryptWallet() {
if (d.exec() == QDialog::Accepted)
{
- QString passphrase = ed.txtPassword->text(); // data comes from user inputs
+ QString passphraseBlank = ed.txtPassword->text(); // data comes from user inputs
+ QString passphrase = QString("HUSH3") + passphraseBlank + QString("SDL");
int length = passphrase.length();
- DataStore::getChatDataStore()->setPassword(passphrase);
+
- char *sequence = NULL;
- sequence = new char[length+1];
- strncpy(sequence, passphrase.toLocal8Bit(), length +1);
+ char *sequence = NULL;
+ sequence = new char[length+1];
+ strncpy(sequence, passphrase.toUtf8(), length +1);
+
+ QString passphraseHash = blake3_PW(sequence);
+ DataStore::getChatDataStore()->setPassword(passphraseHash);
- #define MESSAGE ((const unsigned char *) sequence)
- #define MESSAGE_LEN length
+ char *sequence1 = NULL;
+ sequence1 = new char[length+1];
+ strncpy(sequence1, passphraseHash.toUtf8(), length+1);
- unsigned char hash[crypto_secretstream_xchacha20poly1305_KEYBYTES];
+ #define MESSAGE ((const unsigned char *) sequence)
+ #define MESSAGE_LEN length
+ #define hash ((const unsigned char *) sequence1)
- crypto_hash_sha256(hash,MESSAGE, MESSAGE_LEN);
+ #define PASSWORD sequence
+ #define KEY_LEN crypto_box_SEEDBYTES
- #define PASSWORD sequence
- #define KEY_LEN crypto_box_SEEDBYTES
+ unsigned char key[KEY_LEN];
-
-
- /////////we use the Hash of the Password as Salt, not perfect but still a good solution.
-
- unsigned char key[KEY_LEN];
-
- if (crypto_pwhash
- (key, sizeof key, PASSWORD, strlen(PASSWORD), hash,
- crypto_pwhash_OPSLIMIT_SENSITIVE, crypto_pwhash_MEMLIMIT_SENSITIVE,
- crypto_pwhash_ALG_DEFAULT) != 0) {
- /* out of memory */
+ if (crypto_pwhash
+ (key, sizeof key, PASSWORD, strlen(PASSWORD), hash,
+ crypto_pwhash_OPSLIMIT_SENSITIVE, crypto_pwhash_MEMLIMIT_SENSITIVE,
+ crypto_pwhash_ALG_DEFAULT) != 0) {
+ /* out of memory */
}
+ QString passphraseHash1 = QByteArray(reinterpret_cast(key), KEY_LEN).toHex();
+ DataStore::getChatDataStore()->setPassword(passphraseHash1);
auto dir = QDir(QStandardPaths::writableLocation(QStandardPaths::AppDataLocation));
auto dirHome = QDir(QStandardPaths::writableLocation(QStandardPaths::HomeLocation));
- // QString source_file = dir.filePath("addresslabels.dat");
- // QString target_enc_file = dir.filePath("addresslabels.dat.enc");
QString sourceWallet_file = dirwallet;
QString target_encWallet_file = dirwalletenc;
-
- // FileEncryption::encrypt(target_enc_file, source_file, key);
+
FileEncryption::encrypt(target_encWallet_file, sourceWallet_file, key);
QFile wallet(dirwallet);
- // QFile address(dir.filePath("addresslabels.dat"));
wallet.rename(dirwalletbackup);
- // address.rename(dir.filePath("addresslabels.datBackup"));
QMessageBox::information(this, tr("Wallet Encryption Success"),
QString("Successfully encrypted your wallet"),
@@ -484,27 +461,28 @@ void MainWindow::removeWalletEncryption() {
if (d.exec() == QDialog::Accepted)
{
- QString str = ed.txtPassword->text(); // data comes from user inputs
- int length = str.length();
+ QString passphraseBlank = ed.txtPassword->text(); // data comes from user inputs
+
+ QString passphrase = QString("HUSH3") + passphraseBlank + QString("SDL");
+
+ int length = passphrase.length();
char *sequence = NULL;
sequence = new char[length+1];
- strncpy(sequence, str.toLocal8Bit(), length +1);
+ strncpy(sequence, passphrase.toUtf8(), length +1);
- #define MESSAGE ((const unsigned char *) sequence)
- #define MESSAGE_LEN length
+ QString passphraseHash = blake3_PW(sequence);
- unsigned char hash[crypto_secretstream_xchacha20poly1305_KEYBYTES];
+ char *sequence1 = NULL;
+ sequence1 = new char[length+1];
+ strncpy(sequence1, passphraseHash.toUtf8(), length+1);
- crypto_hash_sha256(hash,MESSAGE, MESSAGE_LEN);
+
+ #define hash ((const unsigned char *) sequence1)
#define PASSWORD sequence
#define KEY_LEN crypto_box_SEEDBYTES
-
-
- /////////we use the Hash of the Password as Salt, not perfect but still a good solution.
-
unsigned char key[KEY_LEN];
if (crypto_pwhash
@@ -513,18 +491,14 @@ void MainWindow::removeWalletEncryption() {
crypto_pwhash_ALG_DEFAULT) != 0) {
/* out of memory */
}
-
-
auto dir = QDir(QStandardPaths::writableLocation(QStandardPaths::AppDataLocation));
auto dirHome = QDir(QStandardPaths::writableLocation(QStandardPaths::HomeLocation));
QString target_encwallet_file = dirwalletenc;
QString target_decwallet_file = dirwallet;
- // QString target_encaddr_file = dir.filePath("addresslabels.dat.enc");
- // QString target_decaddr_file = dir.filePath("addresslabels.dat");
FileEncryption::decrypt(target_decwallet_file, target_encwallet_file, key);
- // FileEncryption::decrypt(target_decaddr_file, target_encaddr_file, key);
+
QFile filencrypted(dirwalletenc);
QFile wallet(dirwallet);
@@ -556,56 +530,54 @@ void MainWindow::removeWalletEncryptionStartUp() {
QDialog d(this);
Ui_startup ed;
ed.setupUi(&d);
-
+
if (d.exec() == QDialog::Accepted)
{
- QString password = ed.txtPassword->text(); // data comes from user inputs
- int length = password.length();
- DataStore::getChatDataStore()->setPassword(password);
+ QString passphraseBlank = ed.txtPassword->text(); // data comes from user inputs
+
+ QString passphrase = QString("HUSH3") + passphraseBlank + QString("SDL");
+ int length = passphrase.length();
+
char *sequence = NULL;
sequence = new char[length+1];
- strncpy(sequence, password.toLocal8Bit(), length +1);
+ strncpy(sequence, passphrase.toUtf8(), length +1);
+
+ QString passphraseHash = blake3_PW(sequence);
+
+
+ char *sequence1 = NULL;
+ sequence1 = new char[length+1];
+ strncpy(sequence1, passphraseHash.toUtf8(), length+1);
#define MESSAGE ((const unsigned char *) sequence)
#define MESSAGE_LEN length
-
- unsigned char hash[crypto_secretstream_xchacha20poly1305_KEYBYTES];
-
- crypto_hash_sha256(hash,MESSAGE, MESSAGE_LEN);
+ #define hash ((const unsigned char *) sequence1)
#define PASSWORD sequence
- #define KEY_LEN crypto_box_SEEDBYTES
+ #define KEY_LEN crypto_box_SEEDBYTES
-
+ unsigned char key[KEY_LEN];
- /////////we use the Hash of the Password as Salt, not perfect but still a good solution.
-
- unsigned char key[KEY_LEN];
-
- if (crypto_pwhash
- (key, sizeof key, PASSWORD, strlen(PASSWORD), hash,
- crypto_pwhash_OPSLIMIT_SENSITIVE, crypto_pwhash_MEMLIMIT_SENSITIVE,
- crypto_pwhash_ALG_DEFAULT) != 0) {
+ if (crypto_pwhash
+ (key, sizeof key, PASSWORD, strlen(PASSWORD), hash,
+ crypto_pwhash_OPSLIMIT_SENSITIVE, crypto_pwhash_MEMLIMIT_SENSITIVE,
+ crypto_pwhash_ALG_DEFAULT) != 0) {
/* out of memory */
- }
+}
+ QString passphraseHash1 = QByteArray(reinterpret_cast(key), KEY_LEN).toHex();
+ DataStore::getChatDataStore()->setPassword(passphraseHash1);
-
- {
auto dir = QDir(QStandardPaths::writableLocation(QStandardPaths::AppDataLocation));
- auto dirHome = QDir(QStandardPaths::writableLocation(QStandardPaths::HomeLocation));
+
QString target_encwallet_file = dirwalletenc;
QString target_decwallet_file = dirwallet;
- // QString target_encaddr_file = dir.filePath("addresslabels.dat.enc");
- // QString target_decaddr_file = dir.filePath("addresslabels.dat");
FileEncryption::decrypt(target_decwallet_file, target_encwallet_file, key);
- // FileEncryption::decrypt(target_decaddr_file, target_encaddr_file, key);
- }
+
auto dirHome = QDir(QStandardPaths::writableLocation(QStandardPaths::HomeLocation));
QFile wallet(dirwallet);
- //QFile backup(dirHome.filePath(".silentdragonlite/silentdragonlite-wallet.datBACKUP"));*/
if (wallet.size() > 0)
{
 ## PRIVACY NOTICE
@@ -15,7 +15,17 @@ This means your IP address is known to these servers. Enable Tor setting in Sile
Go to the releases page and grab the latest installers or binary. https://github.com/MyHush/SilentDragonLite/releases
-### Note Management
+## Install Torsocks (or any other Socks service for TOR) on Ubuntu 18.04
+```
+sudo apt update
+sudo apt install torsocks
+```
+## Connection to our TOR onion service Server
+```
+* Open SDL Edit->Settings->LightwalletServer->rnhk4pwlsbaqzx7wcqfy47lijf2opklstaukq35reiz5rn76crfqpjqd.onion:9067
+* Open the folder of SDL in a Terminal -> Enter: TORSOCKS_LOG_LEVEL=1 torsocks -i ./SilentDragonLite
+```
+## Note Management
SilentDragonLite does automatic note and utxo management, which means it doesn't allow you to manually select which address to send outgoing transactions from. It follows these principles:
* Defaults to sending shielded transactions, even if you're sending to a transparent address
* Sapling funds need at least 2 confirmations before they can be spent
diff --git a/compile.log b/compile.log
deleted file mode 100644
index 6c6584f..0000000
--- a/compile.log
+++ /dev/null
@@ -1,5 +0,0 @@
-Compiling SilentDragonLite 1.2.2 with 4 threads...
-g++ -c -include bin/SilentDragonLite -pipe -g -std=gnu++1y -Wall -W -D_REENTRANT -fPIC -DQT_DEPRECATED_WARNINGS -DQAPPLICATION_CLASS=QApplication -D_FORTIFY_SOURCE=2 -DQT_WIDGETS_LIB -DQT_GUI_LIB -DQT_WEBSOCKETS_LIB -DQT_NETWORK_LIB -DQT_CORE_LIB -I. -Isrc/3rdparty -Isrc -Isingleapplication -Ires -isystem /usr/include/x86_64-linux-gnu/qt5 -isystem /usr/include/x86_64-linux-gnu/qt5/QtWidgets -isystem /usr/include/x86_64-linux-gnu/qt5/QtGui -isystem /usr/include/x86_64-linux-gnu/qt5/QtWebSockets -isystem /usr/include/x86_64-linux-gnu/qt5/QtNetwork -isystem /usr/include/x86_64-linux-gnu/qt5/QtCore -Ibin -Isrc -I/usr/lib/x86_64-linux-gnu/qt5/mkspecs/linux-g++ -o bin/mainwindow.o src/mainwindow.cpp
-g++ -c -include bin/SilentDragonLite -pipe -g -std=gnu++1y -Wall -W -D_REENTRANT -fPIC -DQT_DEPRECATED_WARNINGS -DQAPPLICATION_CLASS=QApplication -D_FORTIFY_SOURCE=2 -DQT_WIDGETS_LIB -DQT_GUI_LIB -DQT_WEBSOCKETS_LIB -DQT_NETWORK_LIB -DQT_CORE_LIB -I. -Isrc/3rdparty -Isrc -Isingleapplication -Ires -isystem /usr/include/x86_64-linux-gnu/qt5 -isystem /usr/include/x86_64-linux-gnu/qt5/QtWidgets -isystem /usr/include/x86_64-linux-gnu/qt5/QtGui -isystem /usr/include/x86_64-linux-gnu/qt5/QtWebSockets -isystem /usr/include/x86_64-linux-gnu/qt5/QtNetwork -isystem /usr/include/x86_64-linux-gnu/qt5/QtCore -Ibin -Isrc -I/usr/lib/x86_64-linux-gnu/qt5/mkspecs/linux-g++ -o bin/sendtab.o src/sendtab.cpp
-g++ -c -include bin/SilentDragonLite -pipe -g -std=gnu++1y -Wall -W -D_REENTRANT -fPIC -DQT_DEPRECATED_WARNINGS -DQAPPLICATION_CLASS=QApplication -D_FORTIFY_SOURCE=2 -DQT_WIDGETS_LIB -DQT_GUI_LIB -DQT_WEBSOCKETS_LIB -DQT_NETWORK_LIB -DQT_CORE_LIB -I. -Isrc/3rdparty -Isrc -Isingleapplication -Ires -isystem /usr/include/x86_64-linux-gnu/qt5 -isystem /usr/include/x86_64-linux-gnu/qt5/QtWidgets -isystem /usr/include/x86_64-linux-gnu/qt5/QtGui -isystem /usr/include/x86_64-linux-gnu/qt5/QtWebSockets -isystem /usr/include/x86_64-linux-gnu/qt5/QtNetwork -isystem /usr/include/x86_64-linux-gnu/qt5/QtCore -Ibin -Isrc -I/usr/lib/x86_64-linux-gnu/qt5/mkspecs/linux-g++ -o bin/addressbook.o src/addressbook.cpp
-g++ -c -include bin/SilentDragonLite -pipe -g -std=gnu++1y -Wall -W -D_REENTRANT -fPIC -DQT_DEPRECATED_WARNINGS -DQAPPLICATION_CLASS=QApplication -D_FORTIFY_SOURCE=2 -DQT_WIDGETS_LIB -DQT_GUI_LIB -DQT_WEBSOCKETS_LIB -DQT_NETWORK_LIB -DQT_CORE_LIB -I. -Isrc/3rdparty -Isrc -Isingleapplication -Ires -isystem /usr/include/x86_64-linux-gnu/qt5 -isystem /usr/include/x86_64-linux-gnu/qt5/QtWidgets -isystem /usr/include/x86_64-linux-gnu/qt5/QtGui -isystem /usr/include/x86_64-linux-gnu/qt5/QtWebSockets -isystem /usr/include/x86_64-linux-gnu/qt5/QtNetwork -isystem /usr/include/x86_64-linux-gnu/qt5/QtCore -Ibin -Isrc -I/usr/lib/x86_64-linux-gnu/qt5/mkspecs/linux-g++ -o bin/addresscombo.o src/addresscombo.cpp
diff --git a/hushchat-screenshot.png b/hushchat-screenshot.png
new file mode 100644
index 0000000..061271d
Binary files /dev/null and b/hushchat-screenshot.png differ
diff --git a/lib/Cargo.lock b/lib/Cargo.lock
index 3c5dbf4..baf8931 100644
--- a/lib/Cargo.lock
+++ b/lib/Cargo.lock
@@ -194,6 +194,20 @@ dependencies = [
"constant_time_eq 0.1.5 (registry+https://github.com/rust-lang/crates.io-index)",
]
+[[package]]
+name = "blake3"
+version = "0.3.4"
+source = "registry+https://github.com/rust-lang/crates.io-index"
+dependencies = [
+ "arrayref 0.3.6 (registry+https://github.com/rust-lang/crates.io-index)",
+ "arrayvec 0.5.1 (registry+https://github.com/rust-lang/crates.io-index)",
+ "cc 1.0.50 (registry+https://github.com/rust-lang/crates.io-index)",
+ "cfg-if 0.1.10 (registry+https://github.com/rust-lang/crates.io-index)",
+ "constant_time_eq 0.1.5 (registry+https://github.com/rust-lang/crates.io-index)",
+ "crypto-mac 0.7.0 (registry+https://github.com/rust-lang/crates.io-index)",
+ "digest 0.8.1 (registry+https://github.com/rust-lang/crates.io-index)",
+]
+
[[package]]
name = "block-buffer"
version = "0.7.3"
@@ -1175,6 +1189,7 @@ dependencies = [
name = "qtlib"
version = "0.1.0"
dependencies = [
+ "blake3 0.3.4 (registry+https://github.com/rust-lang/crates.io-index)",
"lazy_static 1.4.0 (registry+https://github.com/rust-lang/crates.io-index)",
"libc 0.2.66 (registry+https://github.com/rust-lang/crates.io-index)",
"silentdragonlitelib 0.1.0 (git+https://github.com/MyHush/silentdragonlite-cli?rev=d2887d07879a93bdd9b2c8bd12504bb977e82fe0)",
@@ -2461,6 +2476,7 @@ dependencies = [
"checksum bitflags 1.2.1 (registry+https://github.com/rust-lang/crates.io-index)" = "cf1de2fe8c75bc145a2f577add951f8134889b4795d47466a54a5c846d691693"
"checksum blake2b_simd 0.5.10 (registry+https://github.com/rust-lang/crates.io-index)" = "d8fb2d74254a3a0b5cac33ac9f8ed0e44aa50378d9dbb2e5d83bd21ed1dc2c8a"
"checksum blake2s_simd 0.5.10 (registry+https://github.com/rust-lang/crates.io-index)" = "ab9e07352b829279624ceb7c64adb4f585dacdb81d35cafae81139ccd617cf44"
+"checksum blake3 0.3.4 (registry+https://github.com/rust-lang/crates.io-index)" = "423897d97e11b810c9da22458400b28ec866991c711409073662eb34dc44bfff"
"checksum block-buffer 0.7.3 (registry+https://github.com/rust-lang/crates.io-index)" = "c0940dc441f31689269e10ac70eb1002a3a1d3ad1390e030043662eb7fe4688b"
"checksum block-cipher-trait 0.6.2 (registry+https://github.com/rust-lang/crates.io-index)" = "1c924d49bd09e7c06003acda26cd9742e796e34282ec6c1189404dee0c1f4774"
"checksum block-padding 0.1.5 (registry+https://github.com/rust-lang/crates.io-index)" = "fa79dedbb091f449f1f39e53edf88d5dbe95f895dae6135a8d7b881fb5af73f5"
diff --git a/lib/Cargo.toml b/lib/Cargo.toml
index 39a70e9..a0e526e 100644
--- a/lib/Cargo.toml
+++ b/lib/Cargo.toml
@@ -11,4 +11,5 @@ crate-type = ["staticlib"]
[dependencies]
libc = "0.2.58"
lazy_static = "1.4.0"
+blake3 = "0.3.4"
silentdragonlitelib = { git = "https://github.com/MyHush/silentdragonlite-cli", rev = "d2887d07879a93bdd9b2c8bd12504bb977e82fe0" }
diff --git a/lib/silentdragonlitelib.h b/lib/silentdragonlitelib.h
index 4546e70..fdea5db 100644
--- a/lib/silentdragonlitelib.h
+++ b/lib/silentdragonlitelib.h
@@ -13,6 +13,7 @@ extern char * litelib_initialize_new_from_phrase
extern char * litelib_initialize_existing (bool dangerous, const char* server);
extern char * litelib_execute (const char* s, const char* args);
extern void litelib_rust_free_string (char* s);
+extern char * blake3_PW (char* pw);
#ifdef __cplusplus
}
diff --git a/lib/src/lib.rs b/lib/src/lib.rs
index 8be7c55..4ac3bf0 100644
--- a/lib/src/lib.rs
+++ b/lib/src/lib.rs
@@ -29,6 +29,30 @@ pub extern fn litelib_wallet_exists(chain_name: *const c_char) -> bool {
println!("Wallet exists: {}", config.wallet_exists());
config.wallet_exists()
+}
+
+//////hash blake3
+
+#[no_mangle]
+pub extern fn blake3_PW(pw: *const c_char) -> *mut c_char{
+
+ let passwd = unsafe {
+ assert!(!pw.is_null());
+
+ CStr::from_ptr(pw).to_string_lossy().into_owned()
+ };
+
+ let data = passwd.as_bytes();
+// Hash an input all at once.
+let hash1 = blake3::hash(data).to_hex();
+println!("\nBlake3 Hash: {}", hash1);
+
+//let sttring = CString::new(hash1).unwrap();
+let e_str = CString::new(format!("{}", hash1)).unwrap();
+return e_str.into_raw();
+
+
+
}
/// Create a new wallet and return the seed for the newly created wallet.
diff --git a/src/chatmodel.cpp b/src/chatmodel.cpp
index a563398..0b26b3a 100644
--- a/src/chatmodel.cpp
+++ b/src/chatmodel.cpp
@@ -443,43 +443,29 @@ Tx MainWindow::createTxFromChatPage() {
int lengthmemo = memoplain.length();
char *memoplainchar = NULL;
- memoplainchar = new char[lengthmemo+1];
- strncpy(memoplainchar, memoplain.toLocal8Bit(), lengthmemo +1);
-
- /////////We convert the CID from QString to unsigned char*, so we can encrypt it later
- int lengthcid = cid.length();
-
- char *cidchar = NULL;
- cidchar = new char[lengthcid+1];
- strncpy(cidchar, cid.toLocal8Bit(), lengthcid +1);
-
-
-
- QString pubkey = this->getPubkeyByAddress(addr);
- QString passphrase = DataStore::getChatDataStore()->getPassword();
- QString hashEncryptionKey = passphrase;
- int length = hashEncryptionKey.length();
+ memoplainchar = new char[lengthmemo+2];
+ strncpy(memoplainchar, memoplain.toUtf8(), lengthmemo +1);
+ QString pubkey = this->getPubkeyByAddress(addr);
+ QString passphraseHash = DataStore::getChatDataStore()->getPassword();
+ int length = passphraseHash.length();
////////////////Generate the secretkey for our message encryption
- char *hashEncryptionKeyraw = NULL;
- hashEncryptionKeyraw = new char[length+1];
- strncpy(hashEncryptionKeyraw, hashEncryptionKey.toLocal8Bit(), length +1);
+ char *hashEncryptionKeyraw = NULL;
+ hashEncryptionKeyraw = new char[length+1];
+ strncpy(hashEncryptionKeyraw, passphraseHash.toUtf8(), length+1);
#define MESSAGEAS1 ((const unsigned char *) hashEncryptionKeyraw)
#define MESSAGEAS1_LEN length
- unsigned char hash[crypto_kx_SEEDBYTES];
-
- crypto_hash_sha256(hash,MESSAGEAS1, MESSAGEAS1_LEN);
-
+
unsigned char sk[crypto_kx_SECRETKEYBYTES];
unsigned char pk[crypto_kx_PUBLICKEYBYTES];
unsigned char server_rx[crypto_kx_SESSIONKEYBYTES], server_tx[crypto_kx_SESSIONKEYBYTES];
if (crypto_kx_seed_keypair(pk,sk,
- hash) !=0) {
+ MESSAGEAS1) !=0) {
}
////////////////Get the pubkey from Bob, so we can create the share key
@@ -772,29 +758,22 @@ Tx MainWindow::createTxForSafeContactRequest()
QString memo = contactRequest.getMemo();
- // QString privkey = rpc->fetchPrivKey(myAddr);
QString passphrase = DataStore::getChatDataStore()->getPassword();
- QString hashEncryptionKey = passphrase;
- int length = hashEncryptionKey.length();
+ int length = passphrase.length();
////////////////Generate the secretkey for our message encryption
- char *hashEncryptionKeyraw = NULL;
- hashEncryptionKeyraw = new char[length+1];
- strncpy(hashEncryptionKeyraw, hashEncryptionKey.toLocal8Bit(), length +1);
+ char *hashEncryptionKeyraw = NULL;
+ hashEncryptionKeyraw = new char[length+1];
+ strncpy(hashEncryptionKeyraw, passphrase.toUtf8(), length +1);
+
#define MESSAGEAS1 ((const unsigned char *) hashEncryptionKeyraw)
#define MESSAGEAS1_LEN length
-
- unsigned char hash[crypto_kx_SEEDBYTES];
-
- crypto_hash_sha256(hash,MESSAGEAS1, MESSAGEAS1_LEN);
-
-
unsigned char sk[crypto_kx_SECRETKEYBYTES];
unsigned char pk[crypto_kx_PUBLICKEYBYTES];
if (crypto_kx_seed_keypair(pk,sk,
- hash) !=0) {
+ MESSAGEAS1) !=0) {
}
QString publicKey = QByteArray(reinterpret_cast
## PRIVACY NOTICE
@@ -15,7 +15,17 @@ This means your IP address is known to these servers. Enable Tor setting in Sile
Go to the releases page and grab the latest installers or binary. https://github.com/MyHush/SilentDragonLite/releases
-### Note Management
+## Install Torsocks (or any other Socks service for TOR) on Ubuntu 18.04
+```
+sudo apt update
+sudo apt install torsocks
+```
+## Connection to our TOR onion service Server
+```
+* Open SDL Edit->Settings->LightwalletServer->rnhk4pwlsbaqzx7wcqfy47lijf2opklstaukq35reiz5rn76crfqpjqd.onion:9067
+* Open the folder of SDL in a Terminal -> Enter: TORSOCKS_LOG_LEVEL=1 torsocks -i ./SilentDragonLite
+```
+## Note Management
SilentDragonLite does automatic note and utxo management, which means it doesn't allow you to manually select which address to send outgoing transactions from. It follows these principles:
* Defaults to sending shielded transactions, even if you're sending to a transparent address
* Sapling funds need at least 2 confirmations before they can be spent
diff --git a/compile.log b/compile.log
deleted file mode 100644
index 6c6584f..0000000
--- a/compile.log
+++ /dev/null
@@ -1,5 +0,0 @@
-Compiling SilentDragonLite 1.2.2 with 4 threads...
-g++ -c -include bin/SilentDragonLite -pipe -g -std=gnu++1y -Wall -W -D_REENTRANT -fPIC -DQT_DEPRECATED_WARNINGS -DQAPPLICATION_CLASS=QApplication -D_FORTIFY_SOURCE=2 -DQT_WIDGETS_LIB -DQT_GUI_LIB -DQT_WEBSOCKETS_LIB -DQT_NETWORK_LIB -DQT_CORE_LIB -I. -Isrc/3rdparty -Isrc -Isingleapplication -Ires -isystem /usr/include/x86_64-linux-gnu/qt5 -isystem /usr/include/x86_64-linux-gnu/qt5/QtWidgets -isystem /usr/include/x86_64-linux-gnu/qt5/QtGui -isystem /usr/include/x86_64-linux-gnu/qt5/QtWebSockets -isystem /usr/include/x86_64-linux-gnu/qt5/QtNetwork -isystem /usr/include/x86_64-linux-gnu/qt5/QtCore -Ibin -Isrc -I/usr/lib/x86_64-linux-gnu/qt5/mkspecs/linux-g++ -o bin/mainwindow.o src/mainwindow.cpp
-g++ -c -include bin/SilentDragonLite -pipe -g -std=gnu++1y -Wall -W -D_REENTRANT -fPIC -DQT_DEPRECATED_WARNINGS -DQAPPLICATION_CLASS=QApplication -D_FORTIFY_SOURCE=2 -DQT_WIDGETS_LIB -DQT_GUI_LIB -DQT_WEBSOCKETS_LIB -DQT_NETWORK_LIB -DQT_CORE_LIB -I. -Isrc/3rdparty -Isrc -Isingleapplication -Ires -isystem /usr/include/x86_64-linux-gnu/qt5 -isystem /usr/include/x86_64-linux-gnu/qt5/QtWidgets -isystem /usr/include/x86_64-linux-gnu/qt5/QtGui -isystem /usr/include/x86_64-linux-gnu/qt5/QtWebSockets -isystem /usr/include/x86_64-linux-gnu/qt5/QtNetwork -isystem /usr/include/x86_64-linux-gnu/qt5/QtCore -Ibin -Isrc -I/usr/lib/x86_64-linux-gnu/qt5/mkspecs/linux-g++ -o bin/sendtab.o src/sendtab.cpp
-g++ -c -include bin/SilentDragonLite -pipe -g -std=gnu++1y -Wall -W -D_REENTRANT -fPIC -DQT_DEPRECATED_WARNINGS -DQAPPLICATION_CLASS=QApplication -D_FORTIFY_SOURCE=2 -DQT_WIDGETS_LIB -DQT_GUI_LIB -DQT_WEBSOCKETS_LIB -DQT_NETWORK_LIB -DQT_CORE_LIB -I. -Isrc/3rdparty -Isrc -Isingleapplication -Ires -isystem /usr/include/x86_64-linux-gnu/qt5 -isystem /usr/include/x86_64-linux-gnu/qt5/QtWidgets -isystem /usr/include/x86_64-linux-gnu/qt5/QtGui -isystem /usr/include/x86_64-linux-gnu/qt5/QtWebSockets -isystem /usr/include/x86_64-linux-gnu/qt5/QtNetwork -isystem /usr/include/x86_64-linux-gnu/qt5/QtCore -Ibin -Isrc -I/usr/lib/x86_64-linux-gnu/qt5/mkspecs/linux-g++ -o bin/addressbook.o src/addressbook.cpp
-g++ -c -include bin/SilentDragonLite -pipe -g -std=gnu++1y -Wall -W -D_REENTRANT -fPIC -DQT_DEPRECATED_WARNINGS -DQAPPLICATION_CLASS=QApplication -D_FORTIFY_SOURCE=2 -DQT_WIDGETS_LIB -DQT_GUI_LIB -DQT_WEBSOCKETS_LIB -DQT_NETWORK_LIB -DQT_CORE_LIB -I. -Isrc/3rdparty -Isrc -Isingleapplication -Ires -isystem /usr/include/x86_64-linux-gnu/qt5 -isystem /usr/include/x86_64-linux-gnu/qt5/QtWidgets -isystem /usr/include/x86_64-linux-gnu/qt5/QtGui -isystem /usr/include/x86_64-linux-gnu/qt5/QtWebSockets -isystem /usr/include/x86_64-linux-gnu/qt5/QtNetwork -isystem /usr/include/x86_64-linux-gnu/qt5/QtCore -Ibin -Isrc -I/usr/lib/x86_64-linux-gnu/qt5/mkspecs/linux-g++ -o bin/addresscombo.o src/addresscombo.cpp
diff --git a/hushchat-screenshot.png b/hushchat-screenshot.png
new file mode 100644
index 0000000..061271d
Binary files /dev/null and b/hushchat-screenshot.png differ
diff --git a/lib/Cargo.lock b/lib/Cargo.lock
index 3c5dbf4..baf8931 100644
--- a/lib/Cargo.lock
+++ b/lib/Cargo.lock
@@ -194,6 +194,20 @@ dependencies = [
"constant_time_eq 0.1.5 (registry+https://github.com/rust-lang/crates.io-index)",
]
+[[package]]
+name = "blake3"
+version = "0.3.4"
+source = "registry+https://github.com/rust-lang/crates.io-index"
+dependencies = [
+ "arrayref 0.3.6 (registry+https://github.com/rust-lang/crates.io-index)",
+ "arrayvec 0.5.1 (registry+https://github.com/rust-lang/crates.io-index)",
+ "cc 1.0.50 (registry+https://github.com/rust-lang/crates.io-index)",
+ "cfg-if 0.1.10 (registry+https://github.com/rust-lang/crates.io-index)",
+ "constant_time_eq 0.1.5 (registry+https://github.com/rust-lang/crates.io-index)",
+ "crypto-mac 0.7.0 (registry+https://github.com/rust-lang/crates.io-index)",
+ "digest 0.8.1 (registry+https://github.com/rust-lang/crates.io-index)",
+]
+
[[package]]
name = "block-buffer"
version = "0.7.3"
@@ -1175,6 +1189,7 @@ dependencies = [
name = "qtlib"
version = "0.1.0"
dependencies = [
+ "blake3 0.3.4 (registry+https://github.com/rust-lang/crates.io-index)",
"lazy_static 1.4.0 (registry+https://github.com/rust-lang/crates.io-index)",
"libc 0.2.66 (registry+https://github.com/rust-lang/crates.io-index)",
"silentdragonlitelib 0.1.0 (git+https://github.com/MyHush/silentdragonlite-cli?rev=d2887d07879a93bdd9b2c8bd12504bb977e82fe0)",
@@ -2461,6 +2476,7 @@ dependencies = [
"checksum bitflags 1.2.1 (registry+https://github.com/rust-lang/crates.io-index)" = "cf1de2fe8c75bc145a2f577add951f8134889b4795d47466a54a5c846d691693"
"checksum blake2b_simd 0.5.10 (registry+https://github.com/rust-lang/crates.io-index)" = "d8fb2d74254a3a0b5cac33ac9f8ed0e44aa50378d9dbb2e5d83bd21ed1dc2c8a"
"checksum blake2s_simd 0.5.10 (registry+https://github.com/rust-lang/crates.io-index)" = "ab9e07352b829279624ceb7c64adb4f585dacdb81d35cafae81139ccd617cf44"
+"checksum blake3 0.3.4 (registry+https://github.com/rust-lang/crates.io-index)" = "423897d97e11b810c9da22458400b28ec866991c711409073662eb34dc44bfff"
"checksum block-buffer 0.7.3 (registry+https://github.com/rust-lang/crates.io-index)" = "c0940dc441f31689269e10ac70eb1002a3a1d3ad1390e030043662eb7fe4688b"
"checksum block-cipher-trait 0.6.2 (registry+https://github.com/rust-lang/crates.io-index)" = "1c924d49bd09e7c06003acda26cd9742e796e34282ec6c1189404dee0c1f4774"
"checksum block-padding 0.1.5 (registry+https://github.com/rust-lang/crates.io-index)" = "fa79dedbb091f449f1f39e53edf88d5dbe95f895dae6135a8d7b881fb5af73f5"
diff --git a/lib/Cargo.toml b/lib/Cargo.toml
index 39a70e9..a0e526e 100644
--- a/lib/Cargo.toml
+++ b/lib/Cargo.toml
@@ -11,4 +11,5 @@ crate-type = ["staticlib"]
[dependencies]
libc = "0.2.58"
lazy_static = "1.4.0"
+blake3 = "0.3.4"
silentdragonlitelib = { git = "https://github.com/MyHush/silentdragonlite-cli", rev = "d2887d07879a93bdd9b2c8bd12504bb977e82fe0" }
diff --git a/lib/silentdragonlitelib.h b/lib/silentdragonlitelib.h
index 4546e70..fdea5db 100644
--- a/lib/silentdragonlitelib.h
+++ b/lib/silentdragonlitelib.h
@@ -13,6 +13,7 @@ extern char * litelib_initialize_new_from_phrase
extern char * litelib_initialize_existing (bool dangerous, const char* server);
extern char * litelib_execute (const char* s, const char* args);
extern void litelib_rust_free_string (char* s);
+extern char * blake3_PW (char* pw);
#ifdef __cplusplus
}
diff --git a/lib/src/lib.rs b/lib/src/lib.rs
index 8be7c55..4ac3bf0 100644
--- a/lib/src/lib.rs
+++ b/lib/src/lib.rs
@@ -29,6 +29,30 @@ pub extern fn litelib_wallet_exists(chain_name: *const c_char) -> bool {
println!("Wallet exists: {}", config.wallet_exists());
config.wallet_exists()
+}
+
+//////hash blake3
+
+#[no_mangle]
+pub extern fn blake3_PW(pw: *const c_char) -> *mut c_char{
+
+ let passwd = unsafe {
+ assert!(!pw.is_null());
+
+ CStr::from_ptr(pw).to_string_lossy().into_owned()
+ };
+
+ let data = passwd.as_bytes();
+// Hash an input all at once.
+let hash1 = blake3::hash(data).to_hex();
+println!("\nBlake3 Hash: {}", hash1);
+
+//let sttring = CString::new(hash1).unwrap();
+let e_str = CString::new(format!("{}", hash1)).unwrap();
+return e_str.into_raw();
+
+
+
}
/// Create a new wallet and return the seed for the newly created wallet.
diff --git a/src/chatmodel.cpp b/src/chatmodel.cpp
index a563398..0b26b3a 100644
--- a/src/chatmodel.cpp
+++ b/src/chatmodel.cpp
@@ -443,43 +443,29 @@ Tx MainWindow::createTxFromChatPage() {
int lengthmemo = memoplain.length();
char *memoplainchar = NULL;
- memoplainchar = new char[lengthmemo+1];
- strncpy(memoplainchar, memoplain.toLocal8Bit(), lengthmemo +1);
-
- /////////We convert the CID from QString to unsigned char*, so we can encrypt it later
- int lengthcid = cid.length();
-
- char *cidchar = NULL;
- cidchar = new char[lengthcid+1];
- strncpy(cidchar, cid.toLocal8Bit(), lengthcid +1);
-
-
-
- QString pubkey = this->getPubkeyByAddress(addr);
- QString passphrase = DataStore::getChatDataStore()->getPassword();
- QString hashEncryptionKey = passphrase;
- int length = hashEncryptionKey.length();
+ memoplainchar = new char[lengthmemo+2];
+ strncpy(memoplainchar, memoplain.toUtf8(), lengthmemo +1);
+ QString pubkey = this->getPubkeyByAddress(addr);
+ QString passphraseHash = DataStore::getChatDataStore()->getPassword();
+ int length = passphraseHash.length();
////////////////Generate the secretkey for our message encryption
- char *hashEncryptionKeyraw = NULL;
- hashEncryptionKeyraw = new char[length+1];
- strncpy(hashEncryptionKeyraw, hashEncryptionKey.toLocal8Bit(), length +1);
+ char *hashEncryptionKeyraw = NULL;
+ hashEncryptionKeyraw = new char[length+1];
+ strncpy(hashEncryptionKeyraw, passphraseHash.toUtf8(), length+1);
#define MESSAGEAS1 ((const unsigned char *) hashEncryptionKeyraw)
#define MESSAGEAS1_LEN length
- unsigned char hash[crypto_kx_SEEDBYTES];
-
- crypto_hash_sha256(hash,MESSAGEAS1, MESSAGEAS1_LEN);
-
+
unsigned char sk[crypto_kx_SECRETKEYBYTES];
unsigned char pk[crypto_kx_PUBLICKEYBYTES];
unsigned char server_rx[crypto_kx_SESSIONKEYBYTES], server_tx[crypto_kx_SESSIONKEYBYTES];
if (crypto_kx_seed_keypair(pk,sk,
- hash) !=0) {
+ MESSAGEAS1) !=0) {
}
////////////////Get the pubkey from Bob, so we can create the share key
@@ -772,29 +758,22 @@ Tx MainWindow::createTxForSafeContactRequest()
QString memo = contactRequest.getMemo();
- // QString privkey = rpc->fetchPrivKey(myAddr);
QString passphrase = DataStore::getChatDataStore()->getPassword();
- QString hashEncryptionKey = passphrase;
- int length = hashEncryptionKey.length();
+ int length = passphrase.length();
////////////////Generate the secretkey for our message encryption
- char *hashEncryptionKeyraw = NULL;
- hashEncryptionKeyraw = new char[length+1];
- strncpy(hashEncryptionKeyraw, hashEncryptionKey.toLocal8Bit(), length +1);
+ char *hashEncryptionKeyraw = NULL;
+ hashEncryptionKeyraw = new char[length+1];
+ strncpy(hashEncryptionKeyraw, passphrase.toUtf8(), length +1);
+
#define MESSAGEAS1 ((const unsigned char *) hashEncryptionKeyraw)
#define MESSAGEAS1_LEN length
-
- unsigned char hash[crypto_kx_SEEDBYTES];
-
- crypto_hash_sha256(hash,MESSAGEAS1, MESSAGEAS1_LEN);
-
-
unsigned char sk[crypto_kx_SECRETKEYBYTES];
unsigned char pk[crypto_kx_PUBLICKEYBYTES];
if (crypto_kx_seed_keypair(pk,sk,
- hash) !=0) {
+ MESSAGEAS1) !=0) {
}
QString publicKey = QByteArray(reinterpret_cast